Cybersecurity for the Maritime sector
With more than 80% of global trade transported by sea each year, the maritime sector forms a vital link in the global economy.[1] And as the industry embraces digital technologies - integrating IoT technologies, connecting IT and OT systems, and exploring autonomous capabilities - it becomes a bigger target for cyber attacks.
Dutch maritime organizations are at the forefront of this technological evolution. Since the 1980s, the Netherlands has invested heavily in maritime R&D, becoming a global leader in smart shipping and high-tech port infrastructure. But this leadership brings exposure. Threat actors from China, Russia and Iran are well known to target the maritime sector to obtain commercial and/or intellectual advantages, while the Port of Rotterdam lies in the crosshairs of geopolitical conflicts due to its strategic and economic importance.
How can you address this growing threat?
There is this legendary saying on how to overcome your adversaries: 'know thy enemy and know yourself; in a hundred battles, you will never be defeated'. This starts with gaining an understanding of your threat landscape, your adversaries’ intentions, their modus operandi, and specific attacking methods. This page outlines the key threats facing the maritime sector today, along with effective methods for defending against them.
Request a free membership to access our full research insights
Already a member? Login here
Threat landscape
For the maritime industry
Advanced Persistent Threats (APTs)
Tactics, Techniques & Procedures (TTPs)
Attack tools
| Maritime | Maritime + related | Broader focus | All known | |
|---|---|---|---|---|
| APTs | 94 | 121 | 512 | 801 |
| TTPs | 1,674 | 2,123 | 3,541 | 4,112 |
| Attack tools | 1,474 | 1,821 | 3,027 | 3,666 |
Maritime faces more cyber threats than ever
To stay in control becomes more difficult
Data from Hunt & Hackett’s proprietary Threat Diagnostic System shows a marked increase in cyberattacks targeting the maritime sector in recent years - a trend driven by the industry’s strategic, economic, and geopolitical significance. State-sponsored Advanced Persistent Threats (APTs) target maritime organizations to gain access to critical technologies, intellectual property, and sensitive operational data. These attacks are often part of broader geopolitical strategies, aimed at gaining long-term economic and strategic advantages.
At the same time, the sector’s pivotal role in global trade makes it an appealing target for financially motivated threat actors. Ransomware groups and cybercriminals understand that even short-lived disruptions to port operations or shipping schedules can have massive financial consequences, making maritime organizations particularly vulnerable to extortion-based attacks. Adding to this, hacktivists and other politically motivated actors have turned their attention to the sector in recent years, seeking to disrupt maritime operations to send a political message. Together, these threats not only jeopardize the continuity of global trade but also pose serious risks to the safety of crews at sea.
Actor overview
The most active attack groups targeting the maritime sector are shown in the dynamic chart below. This highlights the relationships between the various threat actors, their motivation and their country of origin.
Knowing the APT groups, their motivations and origin countries provides a solid starting point for understanding what you are up against. To get a more comprehensive understanding of the threat landscape, it is important to research, map, and document your adversaries’ intentions to their modus operandi, attack methods and attack tools, as this provides more actionable information for strengthening your defences.
More detailed information on the threat landscape for this sector?
Already a member? Login here
How it works
Threat landscape for the maritime sector
Attacks in the maritime sector
Look down! Look out! Look up!
The following section explores a few selected cyberattacks in the maritime sector in greater detail. These cases highlight the diverse range of threats affecting the industry across multiple countries and sub-sectors. However, they represent only a small fraction of the cyberattacks occurring daily.
January 1, 2022
16:00 PM
DDoS attacks on Dutch ports
2023
In June 2023, the websites of major Dutch ports, including Groningen, Amsterdam, Rotterdam, and Den Helder, were taken offline by coordinated Distributed Denial of Service (DDoS) attacks. Claimed by the pro-Russian hacktivist group NoName057(16), the attacks were retaliation against the Netherlands' decision to purchase Swiss tanks for Ukraine as part of the ongoing Russia-Ukraine conflict. The websites were primarily used as a means of informing the public, rather than for port operations, so the impact was negligible. Nonetheless, this incident shows how maritime infrastructure can become caught in the crosshairs of geopolitical conflicts.[2]
January 1, 2022
16:00 PM
Royal Dirkzwager
2023
In March 2023, Dutch maritime logistics company Royal Dirkzwager suffered an attack by Play ransomware group. The attackers encrypted company systems and exfiltrated sensitive customer data, including email addresses and personal information. Although the ransomware caused minimal operational disruption, the stolen data provided significant leverage for ransom negotiations.[3] Royal Dirkzwager, who supports more than 800 maritime organizations with critical logistical information, publicly apologized for the breach and subsequently implemented enhanced security measures, including Endpoint Detection and Response (EDR) software, to prevent future incidents.[4]
January 1, 2022
16:00 PM
Stena Impero
2019
In July 2019, a UK-flagged product tanker called the Stena Impero was seized by Iranian forces in the Strait of Hormuz after allegedly veering into Iranian waters. Investigations later indicated the vessel's Automatic Identification System (AIS) - used to track ship positions and movements - may have been spoofed, a technique used to manipulate the GPS capabilities of vessels. The incident occurred just 15 days after the British Navy detained the Iranian tanker Grace 1 near Gibraltar and was widely seen as retaliation. While Iran denied tampering with the AIS, this case shows how GPS interference can be used by states to gain geopolitical leverage against their adversaries. Given the fact that AIS spoofing is a relatively low-tech, inexpensive endeavor, it is likely that this tactic will only grow in popularity, particularly as global tensions heighten.[5]
January 1, 2022
16:00 PM
Maersk
2017
In 2017, shipping giant Maersk suffered one of the most significant cyber incidents ever to hit the maritime industry. The NotPetya attack, which initially targeted Ukrainian entities, spread globally through compromised software, claiming victims in more than 60 countries. Maersk was among the hardest hit, losing an enormous chunk of its IT infrastructure thanks to the wiper malware’s destructive capabilities. In fact, the company reported the loss of over 49,000 end-user devices and 1,000 business applications, resulting in damages exceeding $300 million.[6] The attack was eventually attributed to the Russian APT Sandworm, who were working to sabotage and disrupt key Ukrainian entities due to geopolitical tensions between Russia and Ukraine.[7] It appeared that Maersk – like the vast majority of NotPetya's victims – was simply collateral damage. Nonetheless, the impact of this incident was enormous, highlighting the vulnerability of even the industry’s largest, most well-resourced players.
Key Trends
For the maratime sector
The maritime sector is becoming more vulnerable to cyber threats due to several industry-wide trends. Leading the way is a growing reliance on digital technologies, which significantly expands the attack surface. At the same time, aging operational technology and increased IT-OT interconnectivity are introducing new risks. In this section, we take a closer look at the most important trends shaping the threat landscape.
Digitalization introduces new risks for OT systems
Operational Technology (OT) systems, which control crucial physical processes aboard ships and within ports - such as propulsion systems, cargo handling, and navigation - have emerged as attractive targets for cyber attackers. Between 2017 and 2020 alone, cyberattacks on maritime OT systems skyrocketed by 900%, and these attacks have only become more prevalent in the years since.[8]
One of the biggest challenges in securing maritime OT environments is the longevity and diversity of ship equipment. Typically, vessels remain operational for 25-35 years, and updates are done on different pieces of equipment at varying time intervals. Consequently, many OT systems remain unpatched and vulnerable, having been designed in an era when cybersecurity was not a primary concern.[9]
Adding complexity, the maritime sector is rapidly adopting Internet of Things (IoT) technologies to enhance connectivity and collect real-time operational data. Such developments are essential for innovations such as autonomous shipping. However, this increasing digital interconnectivity inadvertently bridges IT and OT networks, amplifying security risks and expanding the potential attack surface.
Complicating matters, maritime operators often face a limited understanding and oversight of their full network and device inventory across fleets and operations. This lack of visibility can lead to hidden vulnerabilities, creating ideal conditions for threat actors seeking to exploit operational weaknesses and disrupt critical maritime functions.[10]
Low frequency, high impact
Cyber risk in the maritime sector is characterized by a "low frequency, high impact" dynamic. While maritime organizations encounter fewer cyber incidents compared to sectors like finance or government, the consequences of a single successful attack can be catastrophic.
For instance, AIS spoofing could mislead a vessel into crashing or grounding, blocking important shipping routes and leading to financial losses, physical damage, and even threats to human life. While not the result of a cyberattack, the 2021 grounding of the EVER GIVEN in the Suez Canal highlighted how quickly a single disruption can ripple across the globe. The six-day blockage brought global trade to a halt, with estimated losses of up to $416 million per hour.[11]
Additionally, attackers could remotely infiltrate vessel engine control systems, causing abrupt engine shutdowns at sea, posing serious safety risks to crew and passengers, and generating significant recovery costs. Equally alarming is the possibility of cyber actors manipulating valves and control systems to release hazardous substances, such as ballast water, oil, or fuel, resulting in environmental disasters.[12]
High-impact scenarios like these show how important it is to adopt robust cybersecurity frameworks within the maritime sector, particularly focusing on safeguarding convergence points between cyber and physical systems.
Delayed awareness and maturity
The maritime sector continues to lag behind other critical infrastructure domains in cybersecurity awareness and preparedness. Despite ongoing digitalization, recognition of the risks posed by increasingly connected systems remains limited. In a 2011 report, ENISA described cybersecurity awareness in the sector as “low to non-existent”- a characterization that still holds weight today.[13] While efforts are underway to improve understanding of cyber threats among maritime professionals, significant gaps remain.
This lack of awareness is mirrored in the sector’s overall cybersecurity maturity. A recent study found that only one in three maritime professionals is confident that their organization's OT security is on par with its IT security, and less than half of surveyed maritime professionals felt their organization's cybersecurity investments were sufficient.[14] This is especially concerning given the sector’s reliance on complex OT systems, which are increasingly being targeted by threat actors. Addressing the dual challenge of raising awareness and improving security maturity is essential to protect maritime operations as digital adoption progresses and cyber threats continue to rise.
NIS2 compliance
For essential and important entities
Many companies in the maritime sector fall under the scope of the NIS2 Directive as Essential or Important entities. Organizations are expected to address several important aspects of cybersecurity, as outlined in Article 21(2) of the Directive, including:
- Awareness of your threat landscape and a data-driven security roadmap
- Risk analysis and security policies to safeguard information systems
- Incident handling and business continuity to ensure resilience and recovery
- Forensic readiness and the ability to perform a root cause analysis
- Supply chain and system security for robust protection and secure development
Hunt & Hackett’s Managed Detection and Response (MDR) solution directly aligns with several of the Directive’s key requirements, including the 24-, 72-, and one month incident reporting timelines, forensic readiness requirements, and risk management preparation. Read on to discover the core features of our service.
Additionally, we've developed a practical assessment framework that aligns NIS2 requirements with established cybersecurity standards, including ISO/IEC 27001:2022, ISO/IEC 27002:2022, and CIS controls. Although exact NIS2 requirements are evolving, our standards-based approach provides a robust foundation to benchmark your current cybersecurity measures and pinpoint areas for improvement.
How to defend yourself
Threat model approach
To defend against this threat landscape, it is equally important to gain critical insights into the current resilience level of your organization. To understand thyself it is useful to let (third-party) security specialists assess your defenses and simulate meaningful attacks. When done right, such an approach provides critical insights into the resilience level of the organization against its threat landscape. Hunt & Hackett use its proprietary threat modelling-based approach with its clients in the manufacturing sector to provide meaningful insights as well as tailored solutions for the strategic, tactical, and operational aspects of their cybersecurity program.
Our approach
Controlling your cybersecurity risks
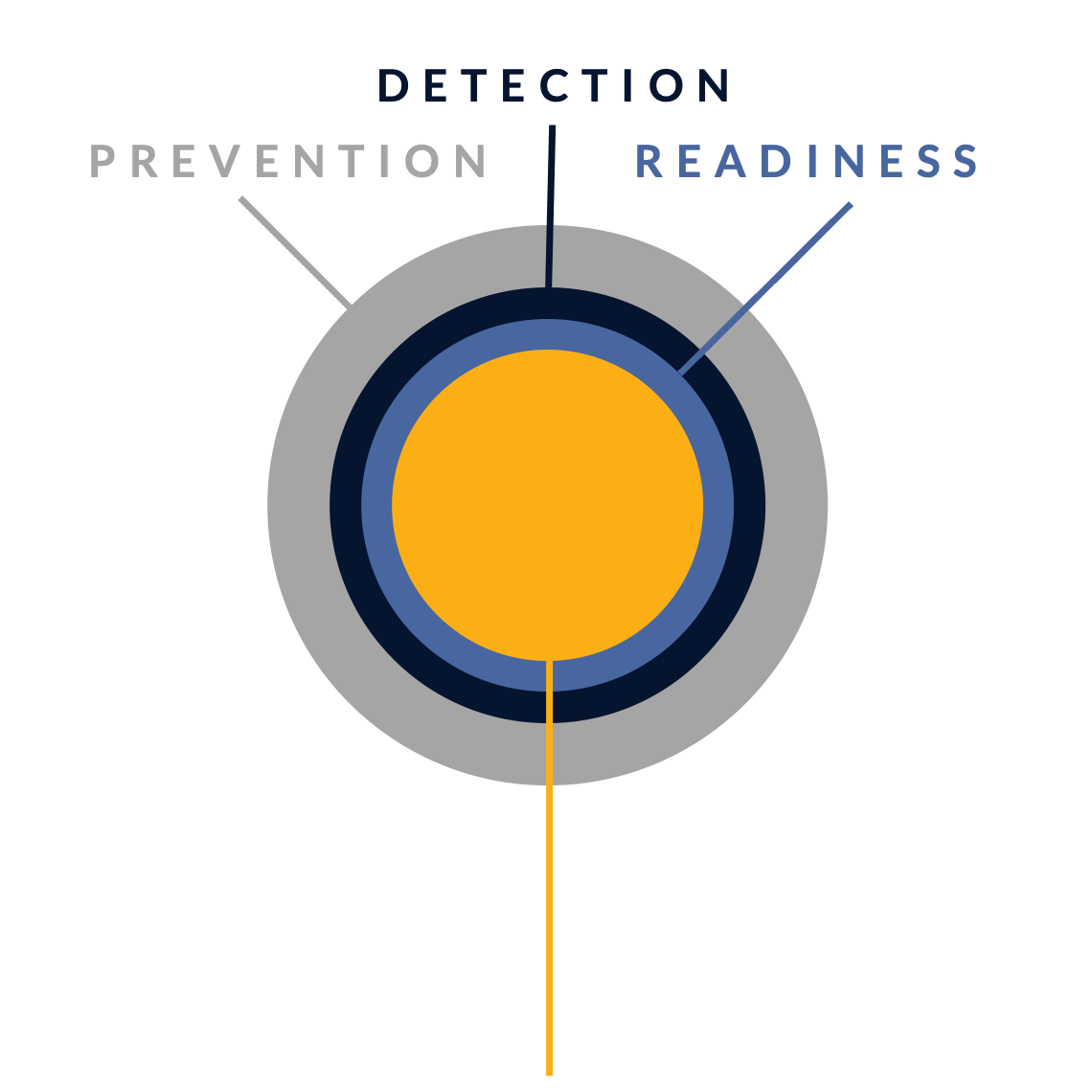
In their fight against cyber attacks, our customers typically go through several stages of maturity. By ramping up their prevention, detection and incident readiness over time – and optimizing this for their actual threat landscape – they reach a point where they have developed solid resilience against targeted attacks, with only highly controlled and accepted risks remaining.
There is no simple 'fix' to become resilient against the sophisticated cyber threats of today. Without serious resources or processes for systematic security activities, protection against modern cyber threats like ransomware is just a wish. Hunt & Hackett has developed a unique threat- and sector-driven approach to cybersecurity, enabling you to work from your current situation to a highly improved and controlled situation, optimized for your specific threat landscape and context as an organisation.
STAGE 1: Unknown risk
Pre-monitoring
-
STAGE 2: Reduced risk
Post-monitoring
-
Detection & response controls
Resilience against non-targeted attacks

STAGE 3: Controlled risk
Implemented roadmap
-
Resilience against non-targeted and semi-targeted attacks
STAGE 4: Highly controlled risk
Targeted attack resilience
-
Our services
Optimized for the maritime industry
Because we use your actual threat landscape and your sector as our starting points, our services are optimised for your specific context and needs.
Managed Detection & Response (MDR)
We detect & react to attacker activity in your environment, minimizing the impact on your business.
Security Program Gap Assessment (SPGA)
We assess your current security program, threat landscape, security controls and risk.
Incident Response (IR)
We help you manage a cyber crisis and contain security incidents, breaches and cyber threats.
Breach & Attack Simulation (BAS)
We validate your security choices by simulating attacks.
Our articles about the maritime sector
From Hunt & Hackett experts
References
2. https://nltimes.nl/2023/06/14/dutch-ports-websites-offline-hours-days-due-pro-russian-cyber-attacks
3. https://therecord.media/royal-dirkzwager-ransomware-attack-dutch-shipping
4. https://dirkzwager.com/news/cyber-security-update/
5. https://www.seatrade-maritime.com/crewing/stena-impero-released-by-iran
6. https://www.missionsecure.com/maritime-security-perspectives-for-a-comprehensive-approach
7. https://www.1kosmos.com/security-glossary/notpetya/
8. https://safety4sea.com/cyber-attacks-on-maritime-ot-systems-increased-900-in-last-three-years/
10. https://www.missionsecure.com/maritime-security-perspectives-for-a-comprehensive-approach
11. https://www.bbc.com/news/business-56559073