Cybersecurity for the Energy sector
The energy sector plays a crucial role in the functioning of modern society. It includes a diverse range of organizations, spanning oil & gas, coal, uranium, nuclear, and renewable energy. Despite their differences, these companies share a common vulnerability: exposure to cyberattacks. In recent years, Hunt & Hackett has seen increased activity from state-aligned and criminal actors targeting the energy sector. This is because of the unique position it occupies at the crossroads of critical infrastructure, national security and geopolitical interests. Threat actors view the sector as a high-value target and know that disruptions to energy infrastructure create powerful leverage to achieve financial and strategic goals. At the same time, the sector is rapidly modernizing to meet growing energy demand. This increases efficiency and scalability but also makes energy systems more technically difficult to secure. Energy companies face a complex task: increase energy availability and meet sustainability goals while safeguarding systems that are critical for national security.
How can you address this growing threat?
There is a legendary saying on how to overcome your adversaries: 'know thy enemy and know yourself; in a hundred battles, you will never be defeated'. To know your enemy starts with gaining an understanding of your threat landscape, your adversaries’ intentions, their modus operandi, and specific attacking methods. The following sections provide a glimpse of the key threats facing the energy sector, followed by our approach to defend against them. The blog series found at the bottom of this page provides a more in-depth analysis of the energy threat landscape.
Request a free membership to access our full research insights
Already a member? Login here
Threat landscape
For the energy industry
Advanced Persistent Threats (APTs)
Tactics, Techniques & Procedures (TTPs)
Attack tools
| Energy | Energy + related | Broader focus | All known | |
|---|---|---|---|---|
| APTs | 137 | 143 | 489 | 801 |
| TTPs | 1,840 | 1,964 | 3,371 | 4,112 |
| Attack tools | 1,732 | 1,823 | 2,931 | 3,666 |
Energy faces more cyber threats than ever
To stay in control becomes more difficult
Our proprietary threat diagnostic system shows an increase in malicious activity targeting the energy sector in recent years. This assessment is supported by data from other leading organizations - Microsoft’s 2025 digital defense report notes that energy is among the top 10 sectors targeted by state-sponsored threat actors[1], while Trustwave reported an 80% year-over-year increase in ransomware attacks against energy and utilities.[2]
This activity can be explained by a few key factors. First, the critical role of energy infrastructure makes the sector vulnerable to extortion. Financially motivated threat actors exploit the sector’s need for continuity and availability, launching ransomware attacks or stealing valuable data to extort payment from their victims. Second, the sector is home to large volumes of high-value R&D which is economically and strategically valuable for less developed nation states, making energy a prime target for espionage and IP theft.
And third, because energy is regarded as critical infrastructure, it is increasingly being targeted in geopolitically motivated attacks. Incidents span all facets of Europe’s energy infrastructure, including underwater and overground gas pipelines and power cables, LNG processing terminals, electricity pylons and substations, offshore oil and gas fields, and solar and wind farms. The ability to sabotage or restrict energy supply is an incredibly powerful tool for states engaged in both physical and hybrid warfare, while pre-positioning in critical systems provides leverage during geopolitical disputes. The North Atlantic Treaty Alliance (NATO) has assessed that the energy sector is one of the biggest targets for cyberattacks, particularly in the context of hybrid warfare activities.[3] Energy infrastructure is an attractive target because disruptions ripple across industries, inflict economic pain, and pose significant societal impacts in affected countries. European supply and demand tread a delicate balance, particularly during winter months, meaning even small disruptions can lead to price spikes, shortages, and increased uncertainty for consumers.[4] The following section, Attacks in the Energy Sector, further examines these factors through the lens of real-world incidents.
Actor overview
The most active attack groups targeting the energy sector are shown in the dynamic chart highlighting the relationships between the various threat actors, their motivations, and their countries of origin.
Knowing the APT groups, their motivations and origin countries provides a solid starting point for understanding what you are up against. To get a more comprehensive understanding of the threat landscape, it is important to research, map, and document your adversaries’ intentions to their modus operandi, attack methods and attack tools, as this provides more actionable information for strenghtening your defences.
More detailed information on the threat landscape for this sector?
Already a member? Login here
How it works
Threat landscape for the energy sector
Attacks in the energy sector
Look down! Look out! Look up!
The following section highlights notable attacks that have impacted the energy sector in recent years. While this selection provides a glimpse into the threat landscape facing energy firms, it represents only a small subset of the cyber activity taking place across the sector. The true scale of attacks remains vast, often unfolding quietly behind the scenes.
January 1, 2022
16:00 PM
Ransomware targets key players in the energy supply chain
2023 & 2024
Recent incidents highlight the prevalence of ransomware attacks in the energy sector. In November 2023, Slovenia’s largest power producer, Holding Slovenske Elektrarne (HSE), fell victim to an attack attributed to Rhysida ransomware group. Corporate systems were temporarily disrupted, but the overall impact was limited: power production continued uninterrupted, and the attack was contained within two days of the initial notification.[5]
Similarly, in December 2024, one of Romania’s largest energy suppliers, Electrica Group, was targeted by ransomware. Once again, the attack led to temporary disruptions in customer services, but crucially, the electricity supply remained unaffected. This was largely due to the isolation of SCADA and other operational technology (OT) systems from the compromised networks. The timing of the incident prompted speculation that there was a geopolitical motive for the attack. Intelligence analysts suggested that it was launched by a pro-Russian group in retaliation for Romania's annulment of its presidential election over alleged Russian interference.[6]
These cases highlight a few important points about ransomware attacks in the energy sector. First, they demonstrate the importance of proper segmentation and isolation of critical systems from general corporate networks. This is especially important for companies like HSE and Electrica, who are major players in their respective countries’ energy supply chains. Second, ransomware is not always profit-driven. The Electrica incident illustrates how financial crime can converge with ideological or strategic motivations, particularly in the context of hybrid warfare.
January 1, 2022
16:00 PM
Espionage campaigns targeting nuclear facilities
2022 & 2024
In addition to disruptive attacks, like ransomware and sabotage, the energy sector is at risk of more subtle, long-term espionage campaigns. A 2024 PWC report noted that espionage posed the highest risk to the sector due to its high-value R&D, which has only been intensified in recent years due to climate-related issues and the impact of geopolitical uncertainties on energy supply.[7]
One such campaign was observed in 2022, when the Russia-linked group Cold River targeted three US nuclear research laboratories. They sought to obtain credentials by creating spoofed login pages for each institution and spear-phishing nuclear scientists. The timing of the campaign revealed a strategic motive, as it coincided with UN inspections of Europe’s largest atomic power plant, located in Russian-controlled Ukrainian territory.[8]
Another espionage campaign targeting the nuclear sector was observed in 2024, when an Iran-linked hacking group known as “Anonymous” breached the IT network of an Israeli nuclear facility, resulting in the theft of thousands of documents including PDFs, emails and presentations. This was one of many cyberattacks launched by Iranian hacking groups against Israel in relation to the conflict in the Gaza Strip. Luckily, the hackers did not appear to gain access to the facility’s operational technology (OT) network, limiting the incident’s impact. Nonetheless, Anonymous sought to ignite panic among Israeli populations living in nearby areas, posting threats and images depicting a nuclear explosion to social media.[9]
January 1, 2022
16:00 PM
Sabotage of Nord Stream gas pipeline
2022
In September 2022, the Nord Stream subsea pipelines were damaged by a series of explosions in the Baltic Sea, near the Danish island of Bornholm. Nord Stream was built by Russia’s state-controlled energy agency Gazprom and consisted of two double-pipelines, Nord Stream 1 (NS1) and Nord Stream 2 (NS2). The explosions ruptured three of the four pipelines, releasing about 800 million cubic meters of gas into the atmosphere – equivalent to three months of Danish gas supply. Authorities concluded that the incident was an act of sabotage by a pro-Ukrainian group, likely in retaliation for the Russian invasion of Ukraine earlier that year.[10] Ukraine has denied involvement in the attack. Germany has since issued arrest warrants for at least six people, including former Ukrainian military officer Serhiy Kuznetsov and Ukrainian diver Volodymyr Zhuravlyov.[11]
The Netherlands was not directly dependent on Nord Stream for its gas supply, but it was indirectly influenced by its role in the European gas market. Crucially, Dutch energy companies and engineering expertise were involved in the ownership, financing, design, and construction of both Nord Stream pipelines.
January 1, 2022
16:00 PM
Geopolitically motivated attacks on renewable energy
2022
The shift towards renewable energy is motivated by more than just sustainability ambitions, but by escalating geopolitical tensions. After the war broke out in Ukraine, many European Member States pledged to consider alternatives to Russian energy imports. Germany, which is Europe’s largest economy, moved up its plan to reach nearly 100% renewable electricity by 2035 and reduce reliance on Russian energy sources. In 2022, 40% of Germany’s natural-gas imports came from Russia.[12]
Naturally, Russia views the shift to renewables as an economic threat. Russian hacking groups working to protect the state’s interests have increasingly targeted European companies in the renewable energy sector. A clear example of this was seen in a spate of attacks throughout 2022, during which at least three German organizations were compromised: Deutsche Windtechnik AG, which specializes in wind turbine maintenance; turbine maker Nordex SE; and Enercon GmbH, another turbine manufacturer who became collateral damage in an attack on the satellite company Viasat.[13] The Danish turbine maker Vestas was also hit by a ransomware attack during the same period. It is believed that Russia-aligned actors were responsible for these attacks. The now disbanded Conti ransomware group, who had ties with Russia’s FSB, claimed responsibility for the attack on Deutsche Windtechnik.[14] As tensions with Russia increase, it’s likely that threat actors will continue to target the renewable energy sector in hopes of undermining Europe’s energy transition and safeguarding Russia’s economy.
January 1, 2022
16:00 PM
Attempted sabotage of the Ukrainian power grid
2015, 2016 & 2022
The attacks on Ukraine’s national power grid are perhaps some of the most sophisticated and disruptive incidents that have occurred in the energy sector. The first of these attacks occurred in 2015, when three power distribution companies in western Ukraine were compromised. The attackers used BlackEnergy malware to collect information from IT and OT platforms over the course of several months, before creating a custom exploit designed to execute the final attack. Two days before Christmas, the attackers started remotely disabling breakers and switchgears of the grids. The malware KillDisk was used to wipe many of the disks in the network, preventing the operators from regaining control.[15] The attack resulted in power outages impacting 225,000 people in Western Ukraine, lasting between one and six hours. This was the first publicly acknowledged successful cyberattack on a national power grid. It was attributed to Sandworm, a sophisticated Advanced Persistent Threat (APT) affiliated with Russia's GRU military intelligence agency.[16]
In 2016, Sandworm returned with another attack on Ukrainian grid operators, resulting in an hour-long electricity disruption in parts of Kyiv. This time the group used Industroyer malware which represented a significant leap in complexity beyond earlier variants like BlackEnergy, boasting autonomous capabilities and the ability to operate even in isolated networks.[17] In 2020, six GRU officers were indicted by the US for their involvement in these and other high-profile cyber campaigns, including NotPetya and Olympic Destroyer.[18]
Nonetheless, another attack followed shortly after the outbreak of war in 2022, when a modified version of the same malware, Industroyer2, was leveraged against a Ukrainian energy supplier. This attack aimed to cause a widespread blackout by shutting down substations, potentially affecting up to two million people. However, the attack was detected and neutralized before it could achieve its full intended impact.[19]
These cases underscore that sabotage of energy systems can be used to support strategic objectives during physical conflicts, as well as highlighting the role of cyberattacks in hybrid warfare. Well-resourced and technically sophisticated actors, like Sandworm, pose a significant threat, and the energy sector will need to adapt accordingly.
Key Trends
For the energy sector
The energy sector operates at the intersection of critical infrastructure and geopolitical interests, making it an attractive target for both state‑aligned and criminal actors. While technological advancements enable more sustainable solutions and meet growing demand, they simultaneously increase interconnectivity and complexity, introducing new vulnerabilities. The following trends highlight key developments shaping the industry and the cybersecurity challenges that come along with them.
Increasing complexity introduces new risks
Energy infrastructure is becoming increasingly interconnected and complex. Digitalization in the sector has led to incredible gains in operational efficiency and scalability but has also increased the number of potential entry points for threat actors, known as the attack surface. Operational Technology (OT) and industrial control systems, which were previously isolated from the Internet and therefore not built with security in mind, are becoming increasingly inter-connected with IT systems, exposing them to new threats.
Meanwhile, the prevalence of decentralized assets, such as electric vehicles, heat pumps and solar PVs connecting to the grid at low voltage levels, adds an additional layer of complexity, making it more difficult to spot security gaps.[20] The result of this is that energy infrastructure is becoming increasingly vulnerable to cyberattacks. This was highlighted by the North American Electric Reliability Corporation (NERC) in 2024, when it warned that the number of susceptible points in US electrical networks was growing by about 60 per day.[21]
Threat actors exploit dependance on third-party vendors
Simultaneously, supply chain vulnerabilities pose a growing risk. Energy infrastructure increasingly relies on third-party software providers, cloud services and imported hardware components, which can be exploited by threat actors hoping to move downstream and gain access to critical data or operational systems. In fact, a recent KPMG report states that the energy sector’s supply chain risks are disproportionately high compared to other sectors: 45% of its cybersecurity breaches originated with third-party vendors, far exceeding the global rate of 29%. Additionally, 67% of energy sector breaches were linked to software and IT providers.[22] Recognising this risk, the NIS2 Directive requires that European organizations evaluate the security practices of all third-party vendors in their supply chains.
The domino effect: Instability across electrical grid connections
The mass power outage that occurred in Portugal and Spain in April 2025 highlights how faults can cascade across electric grid interconnections, resulting in significant disruptions to millions of people. While an investigation found that the blackouts were the result of a rare overvoltage, not a cyberattack, this incident served as a warning of what can happen when abnormalities occur in grid systems.[23] Infrastructure operators should take note and ensure that future cyberattacks cannot intentionally produce the same effects. This is particularly important because Europe’s electricity grid is one of the most interconnected in the world, allowing for cross-border electricity trading and grid balancing, but also enabling sophisticated cyberattacks to potentially spread across multiple Member States.[24]
The nuclear-AI nexus
The increasing integration of AI into the nuclear energy domain is creating a new “nuclear-AI nexus.” For instance, Constellation Energy, North America’s largest nuclear operator, has explored the use of AI to reduce customer energy costs and optimize operations. At the same time, tech giants like Microsoft, Meta, and Google are reportedly considering nuclear power as a sustainable source to fuel future data centers. This blending of AI with nuclear infrastructure introduces a fresh wave of cyber risk, as critical systems become more digitally exposed and interlinked. While no physical sabotage has occurred thus far, the implications are clear: the nexus of nuclear systems and AI, and broader IT–OT convergence, poses elevated potential for cyber-physical disruption.[25]
Hybrid warfare threatens energy resilience
Energy security is increasingly a cyber‑physical challenge. As competition for scarce resources intensifies, adversaries blend supply leverage, physical sabotage and targeted cyber intrusions in hybrid campaigns, often timed to winter demand peaks, while the energy sector remains a primary cyber target. Interconnected grids, pipelines and LNG networks create cross‑border dependencies: diversification of routes and suppliers improves resilience but also broadens the attack surface across vendors and remote‑access paths. In response, operators need to harden third‑party access, segment legacy OT, and continuously monitor OT network and process signals, correlating them with real‑world events (e.g., pipeline outages, sanctions, cable cuts), to spot coordinated campaigns early and prevent cascading outages.[26]
NIS2 compliance
For essential and important entities
Companies in the energy sector fall under the scope of the NIS2 Directive as Essential or Important entities. Organizations are expected to address several important aspects of cybersecurity, as outlined in Article 21(2) of the Directive, including:
- Awareness of your threat landscape and a data-driven security roadmap
- Risk analysis and security policies to safeguard information systems
- Incident handling and business continuity to ensure resilience and recovery
- Forensic readiness and the ability to perform a root cause analysis
- Supply chain and system security for robust protection and secure development
Hunt & Hackett’s Managed Detection and Response (MDR) solution directly aligns with several of the Directive’s key requirements, including the 24-, 72-, and one month incident reporting timelines, forensic readiness requirements, and risk management preparation. Read on to discover the core features of our service.
Additionally, we've developed a practical assessment framework that aligns NIS2 requirements with established cybersecurity standards, including ISO/IEC 27001:2022, ISO/IEC 27002:2022, and CIS controls. Although exact NIS2 requirements are evolving, our standards-based approach provides a robust foundation to benchmark your current cybersecurity measures and pinpoint areas for improvement.
How to defend yourself
Threat model approach
To defend against this threat landscape, it is equally important to gain critical insights into the current resilience level of your organization. To understand thyself it is useful to let (third-party) security specialists assess your defenses and simulate meaningful attacks. When done right, such an approach provides critical insights into the resilience level of the organization against its threat landscape. Hunt & Hackett use its proprietary threat modelling-based approach with its clients in the energy sector to provide meaningful insights as well as tailored solutions for the strategical, tactical, and operational aspects of their cybersecurity program.
Our approach
Controlling your cybersecurity risks
In their fight against cyber attacks, our customers typically go through several stages of maturity. By ramping up their prevention, detection and incident readiness over time – and optimizing this for their actual threat landscape – they reach a point where they have developed solid resilience against targeted attacks, with only highly controlled and accepted risks remaining.
There is no simple 'fix' to become resilient against the sophisticated cyber threats of today. Without serious resources or processes for systematic security activities, protection against modern cyber threats like ransomware is just a wish. Hunt & Hackett has developed a unique threat- and sector-driven approach to cybersecurity, enabling you to work from your current situation to a highly improved and controlled situation, optimized for your specific threat landscape and context as an organisation.
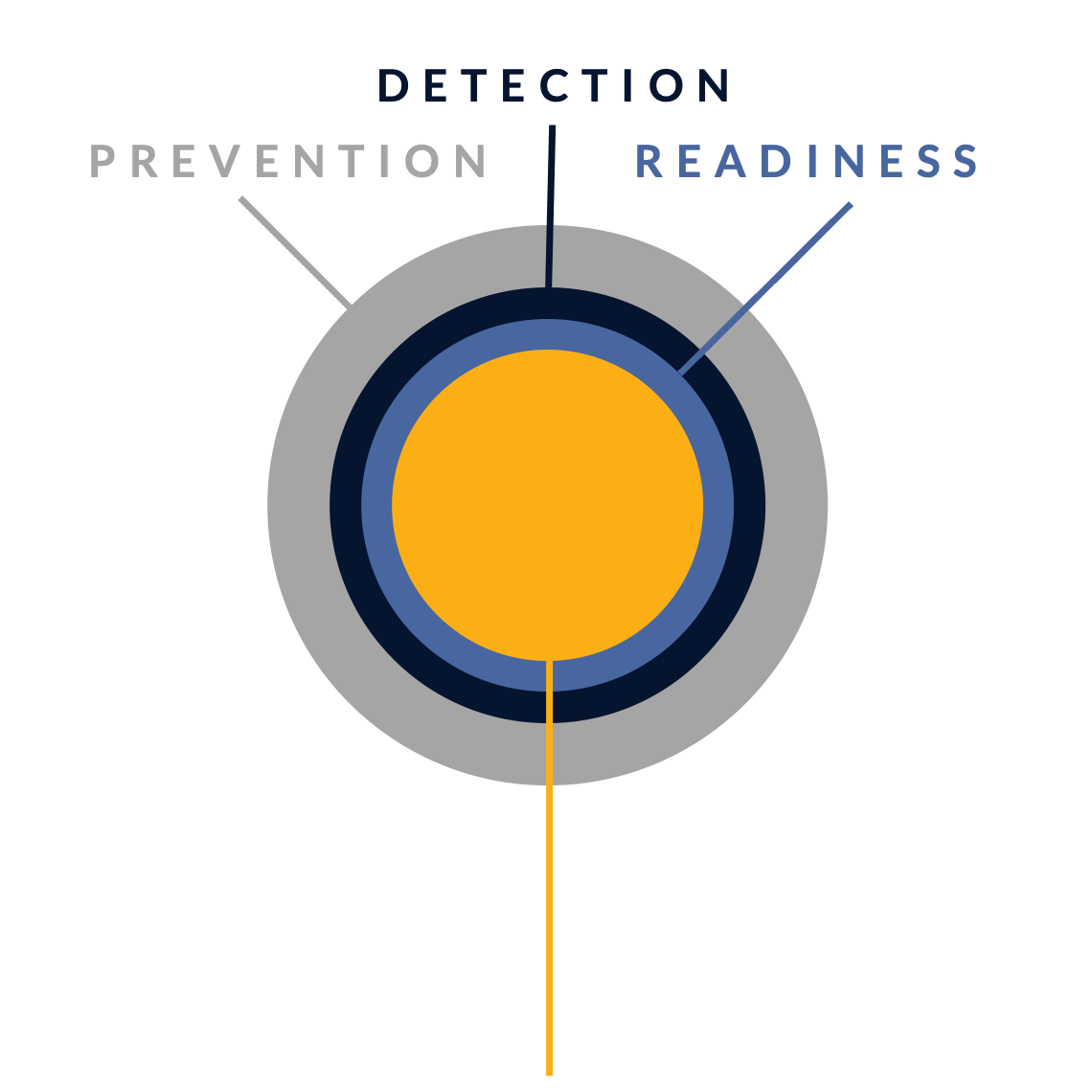
STAGE 1: Unknown risk
Pre-monitoring
-
STAGE 2: Reduced risk
Post-monitoring
-
Detection & response controls
Resilience against non-targeted attacks

STAGE 3: Controlled risk
Implemented roadmap
-
Resilience against non-targeted and semi-targeted attacks
STAGE 4: Highly controlled risk
Targeted attack resilience
-
Our services
Optimized for the energy industry
Because we use your actual threat landscape and your sector as our starting points, our services are optimised for your specific context and needs.
Managed Detection & Response (MDR)
We detect & react to attacker activity in your environment, minimizing the impact on your business.
Security Program Gap Assessment (SPGA)
We assess your current security program, threat landscape, security controls and risk.
Incident Response (IR)
We help you manage a cyber crisis and contain security incidents, breaches and cyber threats.
Breach & Attack Simulation (BAS)
We validate your security choices by simulating attacks.
Our articles about the energy sector
From Hunt & Hackett experts
References
- https://www.microsoft.com/en-us/corporate-responsibility/cybersecurity/microsoft-digital-defense-report-2025/
- https://www.trustwave.com/en-us/resources/blogs/trustwave-blog/trustwave-spiderlabs-ransomware-attacks-against-the-energy-and-utilities-sector-up-80-percent/
- https://www.nato.int/nato_static_fl2014/assets/pdf/2020/12/pdf/201201-Reflection-Group-Final-Report-Uni.pdf
- https://www.reuters.com/business/energy/russian-hybrid-warfare-could-leave-europes-energy-consumers-cold-2025-10-13/
- https://www.darkreading.com/cyberattacks-data-breaches/slovenia-power-provider-hse-suffers-ransomware-attack
- https://securityaffairs.com/171832/hacking/electrica-group-ransomware-attack.html
- https://www.pwc.de/de/energiewirtschaft/under-the-lens-the-energy-sector.pdf
- https://www.reuters.com/world/europe/russian-hackers-targeted-us-nuclear-scientists-2023-01-06/
- https://therecord.media/hackers-claim-attack-on-israeli-nuclear-research-facility
- https://www.reuters.com/world/europe/what-is-known-about-nord-stream-gas-pipeline-explosions-2025-08-21/
- https://www.theguardian.com/business/2025/nov/03/the-nord-stream-riddle-echoes-of-mistrust-ripple-through-europe
- https://www.cyberdaily.au/security/7772-european-wind-energy-sector-hit-in-wave-of-hacks
- https://therecord.media/german-wind-farm-operator-confirms-cybersecurity-incident-after-ransomware-group
- https://www.wired.com/story/conti-ransomware-russia/
- https://www.isa.org/intech-home/2017/march-april/features/ukrainian-power-grids-cyberattack
- https://cyberlaw.ccdcoe.org/wiki/Power_grid_cyberattack_in_Ukraine_(2015)
- https://www.darkreading.com/threat-intelligence/first-malware-designed-solely-for-electric-grids-caused-2016-ukraine-outage
- https://www.justice.gov/archives/opa/pr/six-russian-gru-officers-charged-connection-worldwide-deployment-destructive-malware-and
- https://www.incibe.es/en/incibe-cert/blog/industroyer2-ampere-strikes-back
- https://www.eurelectric.org/in-detail/cybersecurity-in-the-power-sector/
- https://industrialcyber.co/utilities-energy-power-water-waste/resecurity-warns-of-increased-cyber-threats-to-energy-and-nuclear-facilities-from-hacktivists-and-nation-states/#:~:text=Another%20technological%20trend%20that%20has,of%20new%20cyber-risk%20scenarios
- https://www.businesswire.com/news/home/20241023313100/en/67-of-Energy-Sector-Breaches-Linked-to-Software-and-IT-Vendors-SecurityScorecard-Reports
- https://www.weforum.org/stories/2025/05/powering-cyber-resilience-energy-sector/
- https://www.eurelectric.org/in-detail/cybersecurity-in-the-power-sector/
- https://www.resecurity.com/blog/article/cyber-threats-against-energy-sector-surge-global-tensions-mount
- https://www.reuters.com/business/energy/russian-hybrid-warfare-could-leave-europes-energy-consumers-cold-2025-10-13/