Managed Detection & Response (MDR)
Detect & hunt for evidence of attacker activity in your environment
Managed Detection and Response (MDR) encompasses the entire suite of activities performed to guard your security 24 hours per day, 7 days per week.
The service is delivered from our own Security Operations Center (SOC). Here, our experts combine threat intelligence, data-driven analytics and human expertise for the strongest detection and response strategies.
Based on the intelligent threat landscape of your own organization, we monitor each relevant data source (not just what’s relevant in general). This way we’ll help you to quickly outsmart any APT group targeting your assets and ramp up your resilience against ransomware, espionage and other cyber threats.
The Challenge
Monitoring is a continuous process, and only as good as your intelligence and talent.
- Navigating NIS2 compliance
The NIS2 Directive introduces strict cybersecurity standards across the EU, requiring organizations to enhance their cybersecurity with incident reporting, risk management, and continuous monitoring. This adds complexity, as businesses must not only protect against threats but also ensure compliance with evolving regulations—something many find challenging to manage effectively. - Threats go undetected for weeks
Most incidents go undetected for weeks (or even months), due to a lack of threat coverage or false positive alerts. However, if you want to reduce your risk, you need to be able to detect and respond in a matter of hours. -
Access to today’s threat intelligence
The biggest threats are posed by today’s vulnerabilities, not by what happened yesterday. Only if you avail over the latest threat intelligence, you can implement the right measures ‘just in time’.
-
The war for talent
High quality monitoring requires skilled analysts. That’s easier said than done in a world at war for this kind of talent. Remember: analysts thrive on handling incidents – so you’ll likely find the talent you need at expert organizations such as Hunt & Hackett.
The Benefits
Talented people, supported by innovative automation, take the detection of and response to cyberthreats out of your hands. Efficient and scalable.
- Increase resilience against ransomware, espionage and other threats
By investing in MDR, you will decrease the likelihood that serious cyber threats like ransomware will disrupt your business and organisation. -
Forensic & NIS2 readiness
Meet NIS2 requirements with comprehensive log retention and security telemetry, giving you full visibility and readiness for compliance audits. - Proactive threat detection & monitoring
We map threats to your specific data sources for precise monitoring, using an "assume breach" mindset to detect attackers already inside your network. -
Europe's most talented specialists
Our multidisciplinary, talented team of cybersecurity experts monitors your digital footprint day and night. They don’t shy away from an incident and are more than happy to work with you as ‘partners in crime’.
-
Leverages existing investments
Never let a good investment go to waste. Our open technology stack most likely supports your existing detection and response technologies. And if a piece of the puzzle is missing, we will advise on trusted solutions.
Our Approach
Our MDR service is all about building a continuous feedback loop that protects you against ever-changing attack patterns. Intelligence-driven automation plays a crucial role in our approach, to avoid the pitfall of playing a game of 'Whack-a-Mole' to stay in control. If you want to learn more about MDR in general, please have a look at The Definitive Guide to Managed Detection & Response (MDR).
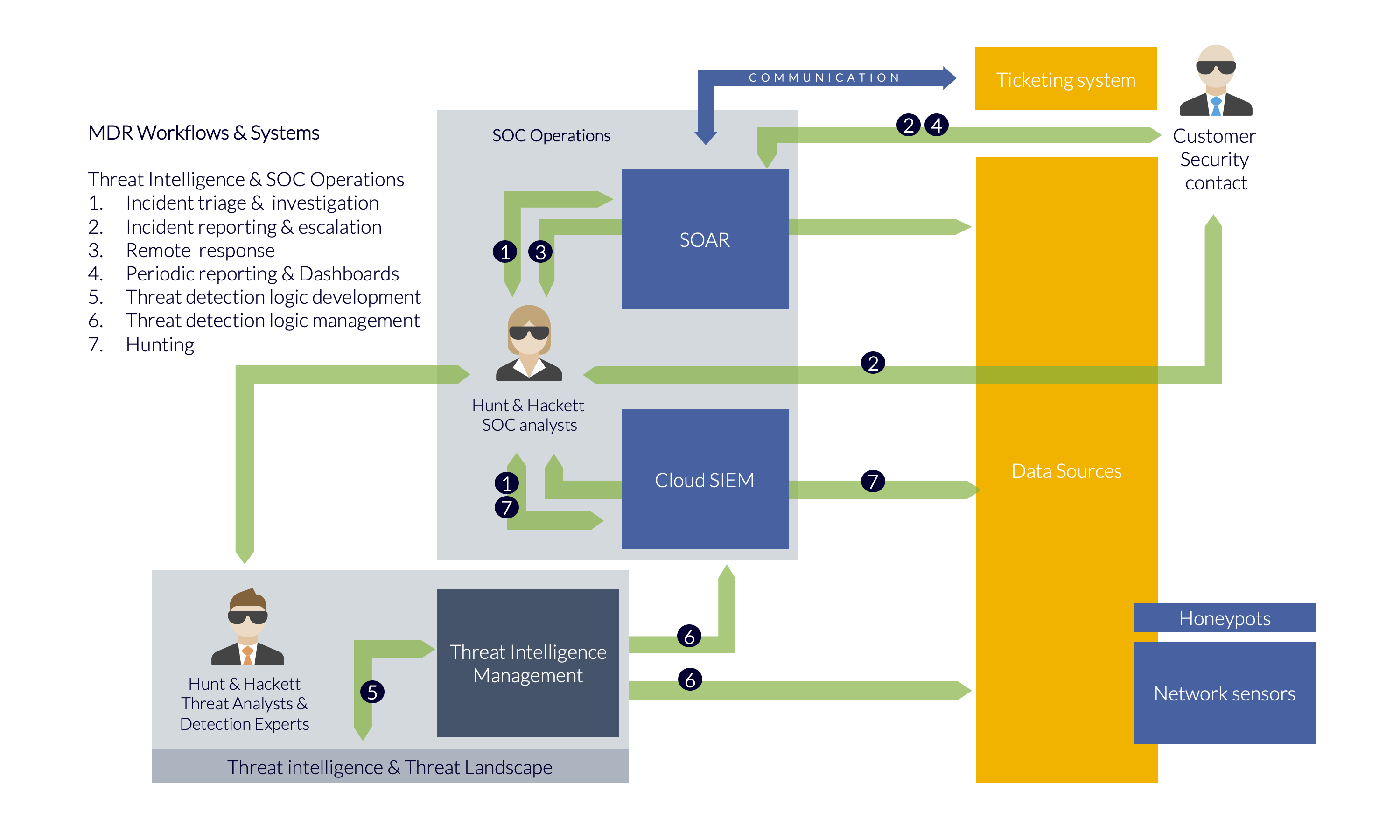
Our MDR platform as solid foundation
We store the security alerts and telemetry* created by your systems in our multi-tenant MDR platform. This platform is designed and built to support our innovative MDR-processes and incorporates trusted technologies such as SOAR (XSOAR), Next-Gen Security Analytics (Google Cloud SecOps) and anomaly detection systems.
Respond, hunt and optimize
Our analysts quickly respond (remotely if required) to incidents to ensure your organization remains in control. However, we don’t sit back and wait for new alerts. On the contrary: we hunt proactively for new threats and update the detection logic of your systems accordingly.
Insights and communication via app and portal
Our customers can contact our analysts, access the security overview and review incidents via our app or our portal.
The next step: Breach & Attack Simulation (BAS)
Once all your systems and processes for MDR are in place, it’s time to further mature your cybersecurity strategies with our Breach & Attack (BAS) services.
* We are technology agnostic and support a broad set of ‘sensors’, including:
- Network: network traffic inspection (ids, ngfw)
- Logs: server and application logs
- Cloud: Azure, Microsoft365 security logs
- Endpoint: Microsoft Defender ATP, LimaCharlie, ESET
If required we advise you on selecting one that’s right for you.
Tailored dashboards
for MDR customers
In addition to the core MDR service, we provide tailored security insights through real-time dashboards using the data already collected in our SIEM. These dashboards provide an additional layer of visibility into customers' environments, showing exactly what’s being logged, where the gaps are, and highlighting legacy protocols or misconfigurations which pose security risks. This enables you to prioritize security improvements in a data-driven manner and proactively address widespread, low-visibility issues. Watch the video below to learn more.
Why Hunt & Hackett?
Your trusted ally in cybersecurity
Skills & Expertise
The Hunt & Hackett team has unrivalled expertise and skills, having recruited the top experts from within the world of cybersecurity, incident response, forensics and operations to operate a SOC.
Methodology
Hunt & Hackett combines both expert analysis of historical forensic evidence and real-time threat detection and hunting, allowing the team to detect attacker activity.
Technology & Tools
The platform allows immediate, real-time visibility into your IT environment, identifying potential compromises and allowing quick action to make sure incidents don’t escalate.
FAQ
Frequently asked questions
How does Hunt & Hackett detect sophisticated attacks that don’t show up in standard dashboards?
We start from an assume-breach, threat-driven model. Using our Threat Intelligence Platform (TIP), we map relevant threat actors → TTPs → tools → controls → data sources → detection coverage for your environment.
On top of native detections (e.g. Defender, Entra, M365, Azure), we run 300+ TTP-driven detections with strong focus on:
- lateral movement and credential abuse
- stealthy persistence and abuse of built-in tooling
- command-and-control and data-exfiltration patterns
Because we keep 12 months of hot, directly searchable telemetry, our SOC and IR teams can reconstruct the full kill chain, not just the initial alert that happened to fire.
Is your MDR really 24/7, and what happens outside office hours?
Yes. Our SOC is staffed 24/7, not just “on-call”.
- During nights and weekends, analysts continue to monitor, triage and respond within agreed SLAs.
- Confirmed or highly likely incidents are contained remotely by default (endpoint isolation, account disable, token revocation, IP/domain blocking, etc.), following a pre-agreed response mandate per asset type.
- For high-severity cases, our IR team can be engaged immediately; on-site presence is available under our paid IR Retainer tiers.
How does Hunt & Hackett prevent SIEM and data costs from exploding?
We built our own ingest optimiser specifically for this problem. In practice, we typically:
- reduce ingest volume by 50–80%,
- while keeping the fields and event types needed for detection, forensics and hunting.
We do this by:
- de-duplicating noisy and repetitive events,
- stripping irrelevant or low-value fields,
- applying threat-led filtering: keep what matters for your attack paths, drop what doesn’t.
On top of that, we continuously monitor ingest patterns and adjust pipelines as your environment and threats evolve, so you keep 12 months of hot telemetry without runaway SIEM ingestion costs.
Ingest and retention assumptions are explicit in our commercial model, so you don’t get unpleasant surprises after go-live.
Do you work with Microsoft Sentinel and Defender or replace them?
Most customers already have significant investments in Microsoft security. We don’t show up and tell you to rip that out. In practice we usually unlock more telemetry than before, not less:
- We keep Microsoft Defender, Entra ID / Azure AD, on-prem Active Directory and M365 as core sensors.
- Together we decide what role Sentinel should keep: stay as-is, be slimmed down, or be phased out once our data lake and pipelines take over the heavy lifting.
The goal is always the same:
- keep the value of your Microsoft investment,
- avoid paying twice for the same telemetry, and
- get deeper detection, hunting and IR than “Sentinel-only” MDR typically provides.
What is included in your MDR fee, and what can be extra?
Included in the MDR fee:
- MDR operations & 24/7 monitoring within the agreed scope.
- Ingest up to the commercially agreed volume.
- TTP-based detection logic & response playbooks (our full global library, tuned to your environment).
- Standard reporting & insights: dashboards, portal/app access and weekly/monthly/quarterly MDR summaries.
- Baseline Incident Response Retainer (Tier 3) for remote containment and best-effort IR support.
- Governance & collaboration: the standard onboarding model, operational check-ins, tactical reviews and strategic sessions as agreed.
- Ad-hoc advice & sounding board: day-to-day questions, design choices and “what do you think of this?” discussions are part of the service, not separate projects.
Potential extras (always scoped and agreed in advance):
- Security Program Gap Assessment (SPGA): aligning prevention, detection and response controls with your threat landscape and risk appetite, and translating this into a future-proof roadmap.
- Extended scope: additional locations, OT/ICS environments or extra data sources beyond the initial agreement.
- Higher ingest / longer hot retention: if you want more telemetry or more than 12 months hot data.
- Paid IR Retainer tiers (Tier 1/2): stricter SLAs, larger prepaid hour blocks and guaranteed on-site response in the EU.
- Breach & Attack Simulation (BAS): validating security controls and MDR coverage in production.
- Bespoke projects: for example complex custom integrations, deep audit/compliance reporting or additional assessments.
How do you help us meet our DORA and NIS2 obligations?
European supervisors now expect continuous monitoring, forensic-ready logging and fast, structured incident reporting, not just a stack of tools and a policy binder. Our MDR is engineered to help you meet those expectations in practice, with evidence you can stand behind in conversations with regulators, auditors and counsel.
Concretely, we help you with:
- Log retention & forensic readiness: We keep 12 months of hot, directly searchable telemetry across your critical identities, endpoints, cloud and networks — so you can reconstruct what happened without ad-hoc log hunting, and support investigations, audits and insurance discussions with hard data instead of assumptions.
- Incident reporting timelines: Our IR-led MDR and DFIR lab help you gather and structure the information needed for initial notifications within 24 hours, structured updates around 72 hours, and a substantiated final report within 1 month — for both NIS2-class incidents and the equivalent staged reporting cycles under DORA.
- Risk-based controls & roadmaps: Through our Security Program Gap Assessment (SPGA) and Breach & Attack Simulation (BAS) we map your threat landscape, attack paths and control gaps, link them to DORA and NIS2 requirements, and translate this into a practical, threat-aligned improvement roadmap.
- Data protection & European sovereignty: Hunt & Hackett is a private Dutch company operating under EU law, NIS2 and GDPR. Our SOC, processes and MDR platform are designed with EU data residency as the default and a clear path towards more sovereign, Europe-anchored security — while remaining fully compatible with major platforms like Microsoft, AWS and GCP.
Articles on MDR
From the Hunt & Hackett experts
Get in touch
Let’s outsmart your digital adversaries now