Cybersecurity for the Manufacturing sector
As a cornerstone of the global economy, the manufacturing sector has long been a target for financially motivated criminals and nation-state actors alike. Industrial espionage itself dates back centuries - some credit the start of the Industrial Revolution to British silk spinner John Lombe, who in the early 18th century stole proprietary equipment designs from an Italian manufacturer. He returned to England and used the stolen knowledge to build the world’s first successful powered continuous production unit, laying the foundations for the modern factory.
Fast forward 300 years, and the threat of having your ideas stolen - or falling victim to other malicious activity - has not only grown but shifted into cyberspace. Today, manufacturers face an unprecedented surge in cyberattacks, from ransomware and Business Email Compromise to data theft and digital espionage. Nation state (sponsored) threat actors from China, Russia, Iran and North Korea are well known to target manufacturing organizations to obtain a commercial and/or intellectual advantage. As the industry continues to modernize and expand, so do the risks - especially if the appropriate defenses are not in place.
How can you address this growing threat?
There is a legendary saying on how to overcome your adversaries: 'know thy enemy and know yourself; in a hundred battles, you will never be defeated'. To know your enemy starts with gaining an understanding of your threat landscape, your adversaries’ intentions, their modus operandi, and specific attacking methods. The following sections provide a glimpse of the key threats facing the manufacturing sector, followed by our approach for defending against them. The blog series which can be found at the bottom of this page provides further details of the manufacturing threat landscape.
Request a free membership to access our full research insights
Already a member? Login here
Threat landscape
For the manufacturing industry
Advanced Persistent Threats (APTs)
Tactics, Techniques & Procedures (TTPs)
Attack tools
| Manufacturing | Manufacturing + related | Broader focus | All known | |
|---|---|---|---|---|
| APTs | 57 | 347 | 379 | 801 |
| TTPs | 1,178 | 3,254 | 3,330 | 4,112 |
| Attack tools | 900 | 2,791 | 2,852 | 3,666 |
Manufacturing faces more cyber threats than ever
To stay in control becomes increasingly difficult
Our proprietary threat diagnostic system shows an increase in malicious activity targeting the manufacturing sector in recent years. In fact, manufacturing faced more ransomware attacks than any other industry in 2024, accounting for 14% of total incidents. Cybercriminals view manufacturing companies as attractive targets for a few key reasons. For one, manufacturers rely on uninterrupted operations - any disruption can lead to millions in lost revenue, making them prime targets for ransomware extortion. Their vast and complex supply chains introduce additional vulnerabilities, where a breach in one company can ripple across an entire industry.
Intellectual property is another major draw, with cybercriminals and nation-state actors seeking to steal proprietary designs and processes for commercial or strategic gain. On top of that, many manufacturers still depend on aging operational technology (OT) systems that were never designed with cybersecurity in mind. As these systems become more connected through digital transformation, they create new entry points for attackers. To stay ahead of these evolving threats, manufacturers must first understand who is targeting them, what they’re after, and the tactics they use.
Actor overview
The most active attack groups targeting the manufacturing sector are shown in the dynamic chart highlighting the relationships between the various threat actors, their motivation and their country of origin.
Knowing the APT groups, their motivations and origin countries provides a solid starting point for understanding what you are up against. To get a more comprehensive understanding of the threat landscape, it is important to research, map, and document your adversaries’ intentions to their modus operandi, attack methods and attack tools, as this provides more actionable information for strenghtening your defences.
More detailed information on the threat landscape for this sector?
Already a member? Login here
How it works
Threat landscape for the manufacturing sector
Attacks in the manufacturing sector
Look down! Look out! Look up!
This section takes a closer look at some notable cyberattacks targeting the manufacturing sector in recent years. These cases highlight the diverse range of threats impacting businesses across multiple countries and subsectors, with cybercriminals using a wide variety of tools and techniques to achieve their objectives. While these cases offer insight into the evolving threat landscape, they represent only a small fraction of the attacks occurring daily.
January 1, 2022
16:00 PM
Duvel
2024
In March 2024, Belgian beer manufacturer Duvel fell victim to a ransomware attack that temporarily halted production across its breweries. The Russian hacking group Stormous is believed to have carried out the attack, encrypting the company’s systems and stealing up to 88 gigabytes of data. Duvel was given 17 days to pay a ransom or the information would be published online. As a precaution, the company shut down operations at all of its Belgian sites and a brewery in Kansas City. Luckily, it had robust backups in place, allowing operations to resume quickly.[7] Ultimately, Duvel chose not to pay the ransom and the stolen data was leaked online - not by Stormous, but by another criminal group, Black Basta, suggesting the data had been sold. The leaked files included employee passport copies and internal company documents.[8]
This incident shows that while backups help restore operations quickly, they don’t always remove a hacker’s leverage. Ransomware actors are increasingly using double extortion tactics, where stolen data is used as blackmail, pressuring companies to pay even when they don’t need decryption. To learn more about the rise of double and triple extortion attacks, read our Definitive Guide to Ransomware.
January 1, 2022
16:00 PM
Advanced Micro Devices
2024
In June 2024, US semiconductor manufacturer Advanced Micro Devices (AMD) suffered a data breach. Sensitive information - including future product details, technical specifications, customer databases, and internal communications - was reportedly stolen by a threat actor known as IntelBroker. AMD quickly confirmed the breach and launched an investigation.[5] However, just a few months later, the company was targeted by IntelBroker again - this time working alongside another criminal group, EnergyWeaponUser. More data was stolen and listed for sale on dark web marketplaces.[6]
As a leading player in the semiconductor industry, AMD - and companies like it – face a high risk of information theft and corporate espionage due to the immense value of their intellectual property. Cutting-edge chip designs are not only crucial for commercial competitiveness but also have national security implications, making them prime targets for both cybercriminals and state-sponsored actors. As this case demonstrates, once a company is on the radar of threat actors, it can quickly become the target of repeated attacks, with stolen data fueling further breaches and increasing long-term risk.
January 1, 2022
16:00 PM
Toyota
2022 - 2023
In February 2022, Toyota’s production lines came to an abrupt standstill—not due to mechanical failure, but because of a cyberattack on its supply chain. The target wasn’t Toyota itself but Kojima Industries, a supplier of plastic parts and electronic components. With Kojima compromised, Toyota had no choice but to shut down all 14 of its domestic factories for one day, undercutting production by about 13,000 vehicles. Fortunately, a backup network between the two companies allowed operations to resume quickly, preventing a larger crisis.[3] Nonetheless, the incident clearly demonstrated how a cyberattack on a single supplier can ripple outwards, causing major disruption to global production lines.
Just 18 months later, Toyota was impacted by another attack - this time targeting its financial services division. Hackers exploited the widely used Citrix Bleed vulnerability to steal sensitive corporate documents, then threatened to leak the data online unless an $8 million ransom was paid. A ransomware group known as Medusa claimed responsibility for the hack.[4]
Looking at these two incidents together, it’s clear that hackers will leverage every angle they can to extort businesses in the manufacturing sector. If they can’t halt production, they search for other pain points, often using sensitive corporate data as leverage. To stay ahead, businesses need to ensure their defenses cover the full spectrum of cyber threats.
Key Trends
For the manufacturing sector
As the manufacturing sector embraces digital transformation, sustainability initiatives, and increased automation, the industry is evolving at an unprecedented pace. While these advancements bring efficiency, scalability, and environmental benefits, they also introduce new cybersecurity challenges. From the growing attack surface created by IoT and cloud adoption to the security risks of IT-OT integration, manufacturers must navigate an increasingly complex threat landscape. The following trends highlight key developments shaping the industry - and the cybersecurity challenges that come along with them.
Digital transformation in manufacturing expands the attack surface
The manufacturing sector is rapidly digitalizing, allowing companies to scale operations with fewer resources. IoT devices, such as smart sensors, are enabling predictive maintenance and continuous quality checks, while robots and autonomous systems are streamlining production and cutting costs. Meanwhile, advancements like digital twins - virtual replicas of a physical products or systems - are accelerating product development, reducing the need for lengthy prototyping processes. These advancements are driving efficiency, allowing manufacturers to scale their operations at an unprecedented rate, but they also expand the attack surface, increasing cyber risks.[9] Every IoT device, cloud-based tool, or automated system adds complexity, providing attackers with more entry points into corporate networks. Without strong security measures, the same technologies driving progress can quickly become major vulnerabilities.[10]
Focus on sustainability is driving the cloud transition
Over the past decade, sustainability has become a major focus in the manufacturing sector, driving companies to adopt more climate-friendly initiatives. One major shift has been the move to cloud computing, which offers significant environmental benefits. According to McKinsey, cloud-powered technologies could eliminate 32 metric gigatons of CO₂ equivalent - nearly half of the reduction required to reach net-zero emissions before 2050.[11] Meanwhile, Accenture research indicates that large-scale migration to the public cloud could be equivalent to taking 22 million cars off the road in terms of carbon impact.[12] With such potential, it’s no surprise that manufacturers see cloud migration as a promising avenue to meet sustainability targets.
However, this transition also brings cybersecurity challenges that cannot be ignored. Moving critical operations and sensitive data to the cloud expands the attack surface, potentially introducing new vulnerabilities and increasing the risk of data breaches. Manufacturers must also ensure their cloud environments comply with industry regulations and data protection laws, adding an additional layer of complexity.[13]
Increasing integration of Operational Technology (OT) and Information Technology (IT) systems exposes companies to new risks
The integration of IT and OT in the manufacturing sector is driving efficiency, automation, and real-time decision-making, but it also introduces significant cybersecurity risks.[14] As traditionally isolated OT systems become more connected to IT networks, they inherit vulnerabilities previously confined to the digital realm. This expanded attack surface allows hackers to exploit weak points, whether through ransomware, supply chain compromises, or direct attacks on critical production systems. Legacy OT infrastructure – which was not built with interconnectivity in mind and therefore often lacks modern security features - becomes an easy entry point, while poor network segmentation enables lateral movement once attackers gain access. Both cybercriminals and nation-state actors alike are increasingly leveraging this vulnerability – according to a 2023 survey, 70% of respondents reported cyberattacks on OT systems compared to just 49% the year before.[15] To learn more about the cyber risks to OT systems, check out our blog, The Evolving Threat of OT: Do You Know Your Weak Spots?
NIS2 compliance
for essential and important entities
Many companies in the manufacturing sector fall under the scope of the NIS2 Directive as Essential or Important entities. Organizations are expected to address several important aspects of cybersecurity, as outlined in Article 21(2) of the Directive, including:
- Awareness of your threat landscape and a data-driven security roadmap
- Risk analysis and security policies to safeguard information systems
- Incident handling and business continuity to ensure resilience and recovery
- Forensic readiness and the ability to perform a root cause analysis
- Supply chain and system security for robust protection and secure development
Hunt & Hackett’s Managed Detection and Response (MDR) solution directly aligns with several of the Directive’s key requirements, including the 24-, 72-, and one month incident reporting timelines, forensic readiness requirements, and risk management preparation. Read on to discover the core features of our service.
Additionally, we've developed a practical assessment framework that aligns NIS2 requirements with established cybersecurity standards, including ISO/IEC 27001:2022, ISO/IEC 27002:2022, and CIS controls. Although exact NIS2 requirements are evolving, our standards-based approach provides a robust foundation to benchmark your current cybersecurity measures and pinpoint areas for improvement.
How to defend yourself
Threat model approach
To defend against this threat landscape, it is equally important to gain critical insights into the current resilience level of your organization. To understand thyself it is useful to let (third-party) security specialists assess your defenses and simulate meaningful attacks. When done right, such an approach provides critical insights into the resilience level of the organization against its threat landscape. Hunt & Hackett use its proprietary threat modelling-based approach with its clients in the manufacturing sector to provide meaningful insights as well as tailored solutions for the strategical, tactical, and operational aspects of their cybersecurity program.
Our approach
Controlling your cybersecurity risks
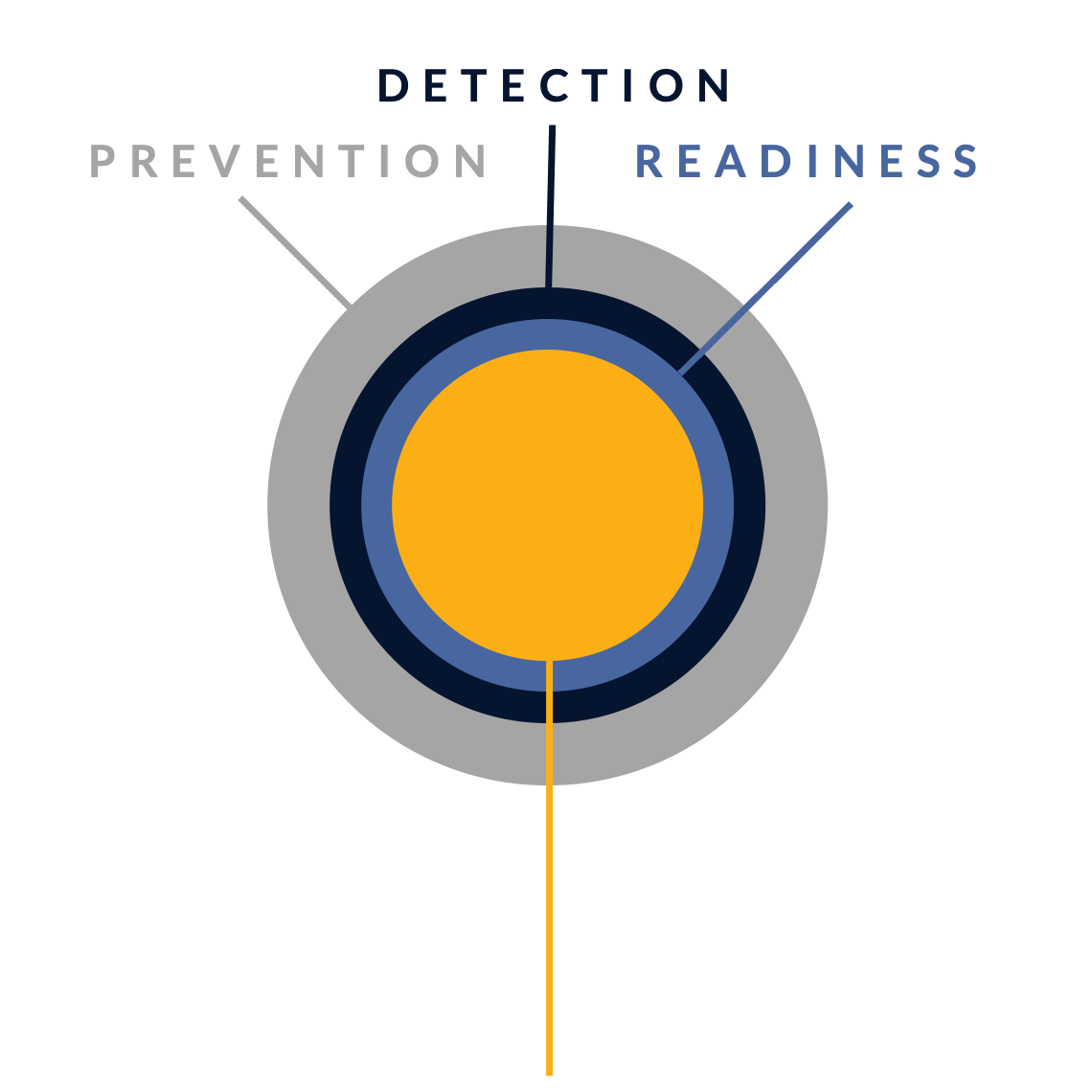
In their fight against cyber attacks, our customers typically go through several stages of maturity. By ramping up their prevention, detection and incident readiness over time – and optimizing this for their actual threat landscape – they reach a point where they have developed solid resilience against targeted attacks, with only highly controlled and accepted risks remaining.
There is no simple 'fix' to become resilient against the sophisticated cyber threats of today. Without serious resources or processes for systematic security activities, protection against modern cyber threats like ransomware is just a wish. Hunt & Hackett has developed a unique threat- and sector-driven approach to cybersecurity, enabling you to work from your current situation to a highly improved and controlled situation, optimized for your specific threat landscape and context as an organisation.
STAGE 1: Unknown risk
Pre-monitoring
-
STAGE 2: Reduced risk
Post-monitoring
-
Detection & response controls
Resilience against non-targeted attacks

STAGE 3: Controlled risk
Implemented roadmap
-
Resilience against non-targeted and semi-targeted attacks
STAGE 4: Highly controlled risk
Targeted attack resilience
-
Our services
Optimized for the manufacturing industry
Because we use your actual threat landscape and your sector as our starting points, our services are optimised for your specific context and needs.
Managed Detection & Response (MDR)
We detect & react to attacker activity in your environment, minimizing the impact on your business.
Security Program Gap Assessment (SPGA)
We assess your current security program, threat landscape, security controls and risk.
Incident Response (IR)
We help you manage a cyber crisis and contain security incidents, breaches and cyber threats.
Breach & Attack Simulation (BAS)
We validate your security choices by simulating attacks.
Our articles about the manufacturing sector
From Hunt & Hackett experts
References
2. https://socradar.io/resources/report/socradar-global-ransomware-report-2024/
4. https://therecord.media/toyota-cyberattack-financial-services-divison
5. https://thecyberexpress.com/amd-data-breach-on-dark-web/
6. https://www.theregister.com/2024/08/26/amd_internal_data_intelbroker/
7. https://therecord.media/stormous-claims-duvel-beer-attack
9. https://www.tmcmedia.nl/en/actueel/de-belangrijkste-trends-in-de-maakindustrie-voor-2025
10. https://experionglobal.com/how-digital-transformation-impacts-cybersecurity/
12. https://www.accenture.com/nl-en/blogs/insights/cloud-trends
13. https://www.sentinelone.com/cybersecurity-101/cloud-security/security-risks-of-cloud-computing/
14. https://axiomcan.com/how-it-ot-integration-is-revolutionizing-the-manufacturing-industry/
15. https://www.fortinet.com/content/dam/fortinet/assets/reports/report-state-ot-cybersecurity.pdf