Cybersecurity for Governments
With the seismic shifts in the geopolitical landscape, Hunt & Hackett has observed a notable increase in the activity of Advanced Persistent Threat (APT) groups targeting the public sector. In recent years, these developments have created a more complex and dynamic threat landscape, where state and non-state actors are increasingly intertwined, consolidating their activities and tactics to undermine the performance of governmental organizations. This trend has also been highlighted by leading security and intelligence agencies in the Netherlands, including the NCSC, AIVD, and MIVD. Erik Akerboom, head of the AIVD, recently emphasized that “criminal actors often overlap with state actors” and that cyber threats to Dutch organizations are on the rise.
Since the Netherlands is known for its highly digitalized society and fulfills, after Germany, the role as the second largest European importer and distributor of goods, it is has become an appealing target for threat actors seeking to digitally paralyze public institutions and steal or leak confidential data.
How can you address this growing threat?
There is this legendary saying on how to overcome your adversaries: “know thy enemy and know thyself; in a hundred battles, you will never be defeated.” Knowing your enemy starts with gaining an understanding of your specific threat landscape, your adversaries’ intentions, their modus operandi, and specific attacking methods. The following sections provide a glimpse of the (central) government specific threat landscape, highlighting trends, upcoming challenges and obstacles, followed up by the Hunt & Hackett approach on how to become more resilient.
Request a free membership to access our full research insights
Already a member? Login here
Threat landscape
For governments
Advanced Persistent Threats (APTs)
Tactics, Techniques & Procedures (TTPs)
Attack tools
| Governments | Governments + related | All known | |
|---|---|---|---|
| APTs | 496 | 515 | 801 |
| TTPs | 3,421 | 3,554 | 4,112 |
| Attack tools | 3,125 | 3,208 | 3,666 |
Government organizations face more cyber threats than ever
To stay in control becomes increasingly difficult
Over the last three years, the Dutch General Intelligence and Security Service (AIVD) has observed a steep growth in the number of countries who have developed offensive cyber programs. Although these programs aren’t as advanced as, for example, the Chinese, Russian, Iranian or North-Korean approaches, the fact that more and more state actors are taking concrete steps towards an offense attitude means that the Dutch public sector is facing digital challenges on a new scale. Even allies are known to engage in espionage against Western nations, with government institutions often being a primary target.
Besides motivations driven by information theft or espionage, Dutch governmental organizations are becoming a target of APTs motivated by hacktivism which is the use of hacking techniques to promote political, social or ideological causes. The national position of the Dutch government in, for example, the Russia-Ukraine war or the situation in Gaza, could be used as a justification for APTs to disrupt the digital infrastructure of public institutions. Hunt & Hackett’s Threat Diagnostic System helps public and semi-public organizations to gain a deeper understanding of who, how and why their organizations are being targeted, as well as on how to address these threats.
Actor overview
The most active attack groups targeting government organizations are shown in the dynamic chart highlighting the relationships between the various threat actors, their motivation and their country of origin.
Knowing the APT groups, their motivations and origin countries provides a solid starting point for understanding what you are up against. To get a more comprehensive understanding of the threat landscape, it is important to research, map, and document your adversaries’ intentions to their modus operandi, attack methods and attack tools, as this provides more actionable information for strenghtening your defences.
More detailed information on the threat landscape for this sector?
Already a member? Login here
How it works
Threat landscape for governments
Attacks in the public sector
Look down! Look out! Look up!
The public sector is one of the most targeted and attacked sectors worldwide. According to data from the European Repository of Cyber Incidents (EuRepoC), governmental organizations and public institutes are still the most common target entities for APTs in 2025.[6] The large volume of sensitive information in this sector makes it an attractive target for cybercrime.
Furthermore, the amount of data circulating within this sector is quite fragmented. Healthcare professionals often work for multiple care providers and across different sectors. They use various information systems, and each system is designed to support the specific care process of the organization it belongs to. Information therefore often does not align with the needs or working methods of the next healthcare professional in the chain which hinders smooth data transfer and keeping up with the newest technological developments.[7]
This challenge is something APTs are taking advantage of. The following section provides a brief overview of striking cyber incidents within the Dutch public sector. However, it is important to bear in mind that these attacks represent only a fraction of the cyber activity taking place in this sector, especially when you look at it on a global scale.
January 1, 2022
16:00 PM
Breach of the Dutch Public Prosecution Service
2025
On July 17, the Dutch Public Prosecution Service (OM) took the precautionary step of disconnecting all internal systems from the internet after the National Cyber Security Center (NCSC) warned of a critical Citrix NetScaler zero-day vulnerability (CVE-2025-6543). Subsequent investigations confirmed that several Citrix systems belonging to the OM had been compromised, though no evidence of data theft or manipulation was reported. Going offline had a significant operational impact - while internal communication channels remained functional, external emailing was halted, and OM staff had to revert to using analogue methods while the phased restoration and recovery was carried out. Speed cameras across the country were also taken offline, with the impact lasting several weeks. Media reports suggest that the attack was likely conducted by Russian hackers, but there has been no official attribution at the time of writing.[8]
January 1, 2022
16:00 PM
A chaotic spring for public websites and administrative portals
2025
In May of 2025, 14 websites of municipalities and provinces in the Netherlands were the victims of DDos-attacks, executed by the pro-Russian hacktivist group called NoName 057(16).[9] NoName has been active since the invasion of Ukraine in 2022 and mainly attacks companies and governmental organizations showing support for the Ukrainian cause. Although these DDoS attacks aren’t motivated by information theft but by ideology - with the goal of causing disruption and attracting attention - they can still have serious consequences. For example, in March the Dutch identity management platform DigiD was also confronted with a similar DDos-attack[10] which resulted in citizens being unable to log in to websites of the Belastingdienst (which was inconvenient considering the timing of the annual tax declaration), UWV (Employee Insurance Agency), DUO (Education implementation service), and various digital patient environments of hospitals. Due to continuous geopolitical unrest, it looks like we will be confronted more and more with these forms of disruptions.
January 1, 2022
16:00 PM
The Dutch National Police
2024
In September 2024, the Dutch National Police suffered from a hack during which employee contact details were stolen. The data included information of public and private partners as well as foreign investigation services. Since the AIVD and MIVD already supported the police with their information security, these intelligence services identified the incident and informed the police. Although until today, there exists some ambiguity about the brains behind this cyber-attack, both Dutch intelligence services argue it is very likely the incident was initiated by a Russian state-sponsored actor known as Laundry Bear.[12]
January 1, 2022
16:00 PM
University Medical Center Groningen
2023
In 2024, the number of cyber incidents targeting the Dutch healthcare sector increased by a striking 160%,[13] driven by a surge in ransomware attacks. In January 2023, the renowned University Medical Center Groningen (UMCG), was the victim of a coordinated Russian cyberattack executed by the pro-Russian hacker group Killnet. As a result of the operation, the official website of the UMCG was shut down for a whole weekend, making it impossible for visitors to access the site. Although UMCG stated that the medical files of patients weren’t affected by the incident, the attack initiated a debate within the national government about the state of digital resilience of Dutch healthcare organizations. This debate resulted in an additional set of action points formulated in the Dutch Cybersecurity Strategy 2022-2028.[14] Despite the fact steps are being taken to increase the awareness of robust cybersecurity measures within this sector, insights into the dynamic threat landscape are often lacking, which makes it difficult to implement the appropriate measures to tackle the activities of threat actors.
January 1, 2022
16:00 PM
COATHANGER - Dutch Ministry of Defense
2023
In 2023, the Dutch Ministry of Defense was impacted by a suspicious network intrusion. Although damage was limited due to prior network segmentation, red flags raised immediately, and the incident received a decent amount of media coverage within and outside of the Netherlands. Initial access occurred through exploitation of the CVE-2022-42475 vulnerability in FortiGate, after which COATHANGER (a second-stage malware) was deployed. The Dutch intelligence agencies MIVD and AIVD attributed the attack with high confidence to a state-sponsored actor from China, as part of broader political espionage efforts. The malware appeared to be selectively deployed after large-scale scanning for vulnerable systems. Organizations using FortiGate devices were advised to follow specific detection and response steps outlined in an official report released by the MIVD and AIVD in 2024 and were strongly advised to apply security patches to internet-facing devices.[15]
Key Trends
For the public sector
In an era marked by rapid digital transformation and increasingly sophisticated cyber threats, the public sector stands at a critical crossroads. Governmental organizations and public institutions are not only keepers of sensitive citizen data but also prime targets for cyberattacks aiming to disrupt essential services and undermine public trust.
Recent trends highlight a surge in ransomware attacks, the growing threat of nation-state actors, and the exploitation of vulnerabilities in legacy systems.[16] At the same time, regulatory frameworks, such as the NIS2 Directive, and international collaboration are becoming more prominent, shaping how governments respond to emerging threats. The section below outlines key trends shaping cybersecurity for the public sector.
The Dutch public sector as an ideological target
In the last couple of years, Dutch public institutes and public organizations have been confronted with an increase in cyberattacks driven by ideological motivations. As mentioned earlier on this page, the Netherlands' political and military support for Ukraine in its war against Russia has made Dutch public institutions and organizations more prominent targets for cyberattacks, particularly from pro-Russian hacker groups. This national stance reflected in aid, sanctions against Russia, and NATO cooperation, has led to an increase in politically motivated cyber threats, including DDoS attacks, phishing campaigns, and espionage efforts. These cyberattacks are often intended to disrupt services, undermine public trust, or retaliate against the Dutch government's foreign policy.[17]
Blurring lines between nation-state actors and cybercriminal groups
In 2024, the distinction between nation-state actors and cybercriminal groups continued to erode, as governments increasingly relied on criminal proxies to carry out disruptive cyber operations with plausible deniability. Groups like North Korea’s Andariel and Iran-backed threat actors collaborated with ransomware affiliates to target foreign organizations, blending financial motives with strategic goals. Leaked communications and high-profile breaches—such as the Conti group’s ties to Russian state actors and China’s iSoon leak—further reveal deepening coordination between cybercriminals and state-sponsored APTs. As geopolitical tensions rise, this convergence is expected to intensify in 2025 and beyond.[18]
Struggling to keep pace with AI developments
Implementing AI and robust cybersecurity strategies within Dutch public institutes faces several challenges. One major difficulty is balancing innovation with strict data protection and privacy regulations, such as the AVG (GDPR). Public institutions must ensure that AI systems are transparent, explainable, and compliant - requirements that can slow down adoption. Additionally, there is often a lack of in-house expertise and resources to develop or manage advanced AI tools securely. Concerns about bias, accountability, and the reliability of automated decision-making also contribute to cautious implementation, creating a tension between the potential of AI and the responsibility of public governance.[19]
How to defend yourself
threat model approach
To defend against this threat landscape, it is equally important to gain critical insights into the current resilience level of your organization. To understand thyself it is useful to let (third-party) security specialists assess your defenses and simulate meaningful attacks. When done right, such an approach provides critical insights into the resilience level of the organization against its threat landscape. Hunt & Hackett use its proprietary threat modelling-based approach with its clients in the government sector to provide meaningful insights as well as tailored solutions for the strategical, tactical, and operational aspects of their cybersecurity program.
Our approach
Controlling your cybersecurity risks
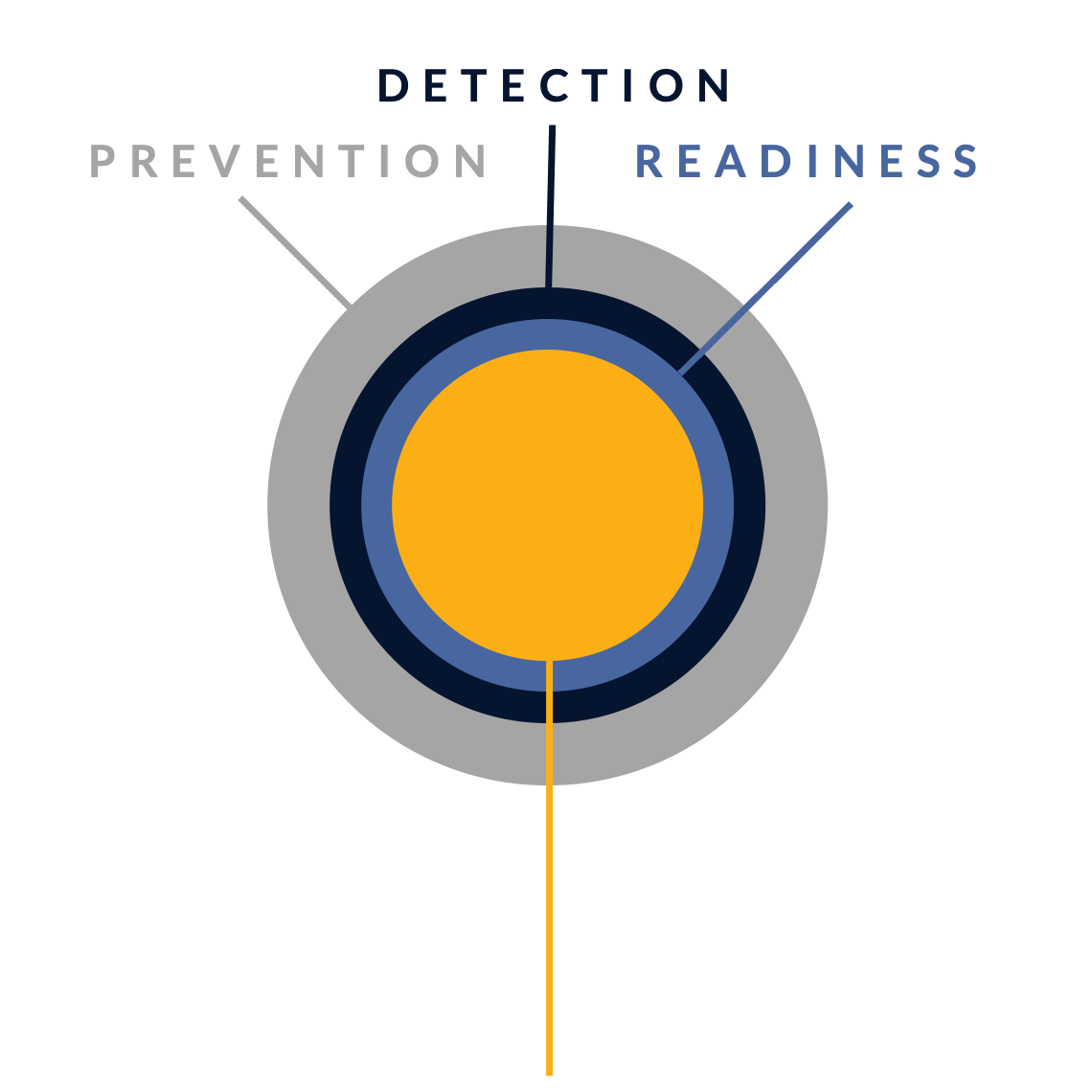
In their fight against cyber attacks, our customers typically go through several stages of maturity. By ramping up their prevention, detection and incident readiness over time – and optimizing this for their actual threat landscape – they reach a point where they have developed solid resilience against targeted attacks, with only highly controlled and accepted risks remaining.
There is no simple 'fix' to become resilient against the sophisticated cyber threats of today. Without serious resources or processes for systematic security activities, protection against modern cyber threats like ransomware is just a wish. Hunt & Hackett has developed a unique threat- and sector-driven approach to cybersecurity, enabling you to work from your current situation to a highly improved and controlled situation, optimized for your specific threat landscape and context as an organisation.
STAGE 1: Unknown risk
Pre-monitoring
-
STAGE 2: Reduced risk
Post-monitoring
-
Detection & response controls
Resilience against non-targeted attacks

STAGE 3: Controlled risk
Implemented roadmap
-
Resilience against non-targeted and semi-targeted attacks
STAGE 4: Highly controlled risk
Targeted attack resilience
-
Our services
Optimized for governments
Because we use your actual threat landscape and your sector as our starting points, our services are optimised for your specific context and needs.
Managed Detection & Response (MDR)
We detect & react to attacker activity in your environment, minimizing the impact on your business.
Security Program Gap Assessment (SPGA)
We assess your current security program, threat landscape, security controls and risk.
Incident Response (IR)
We help you manage a cyber crisis and contain security incidents, breaches and cyber threats.
Breach & Attack Simulation (BAS)
We validate your security choices by simulating attacks.
Our articles about the government sector
From Hunt & Hackett experts
References
- https://english.nctv.nl/latest/news/2024/10/28/cybersecurity-assessment-2024-turbulent-times-unforeseen-effects
- https://www.curacaochronicle.com/post/main/nl-intelligence-service-wants-to-do-more-against-cyber-attacks/
- https://www.cbs.nl/nl-nl/nieuws/2024/17/nederland-tweede-goederenhandelaar-van-de-eu
- https://open.overheid.nl/documenten/18bd22f2-66e3-4a3f-b480-6cfc39b7b879/file
- https://www.cyfirma.com/research/cyber-espionage-among-allies-strategic-posturing-in-an-era-of-trade-tensions/
- https://www.swp-berlin.org/en/swp/about-us/organization/swp-projects/european-repository-on-cyber-incidents-eurepoc
- https://www.tweedekamer.nl/kamerstukken/brieven_regering/detail?id=2023Z06181&did=2023D14649
- https://nltimes.nl/2025/07/21/dutch-prosecution-service-faces-weeks-long-internet-outage-cyber-breach
- https://nos.nl/artikel/2565889-ruim-vijftig-websites-nederland-deze-week-doelwit-pro-russische-hackersgroep
- https://nos.nl/artikel/2560424-digid-opnieuw-tijdelijk-onbereikbaar-geweest-door-ddos-aanval
- https://www.politie.nl/nieuws/2024/november/8/stand-van-zaken-onderzoek-en-veiligheidsmaatregelen-datalek-politie.html
- https://www.defensie.nl/actueel/nieuws/2025/05/27/onbekende-russische-groep-achter-hacks-nederlandse-doelen
- https://www.dutchhealthhub.nl/artikelen/cyberafpersing-in-de-zorg-laat-alarmerende-stijging-zien
- https://www.ncsc.nl/over-ncsc/documenten/publicaties/2022/oktober/10/actieplan-nederlandse-cybersecuritystrategie-2022-2028
- https://www.ncsc.nl/documenten/publicaties/2024/februari/6/mivd-aivd-advisory-coathanger-tlp-clear
- https://reports.weforum.org/docs/WEF_Global_Cybersecurity_Outlook_2025.pdf
- https://open.overheid.nl/documenten/18bd22f2-66e3-4a3f-b480-6cfc39b7b879/file
- https://www.huntandhackett.com/hubfs/downloads/2025_trend_report.pdf
- https://www.rijksoverheid.nl/actueel/nieuws/2025/04/29/nederland-trekt-financiering-voor-ai-data-cloud-en-cybersecurity-innovatie-aan