Cybersecurity for the Logistics sector
Over the past few years Hunt & Hackett has observed a discerning increase in the activity of Advanced Persistent Threat (APT) groups in the logistics sector. Logistics has long been the backbone of global trade, seamlessly connecting economies and ensuring the smooth flow of goods. But as the industry rapidly digitizes, it has become an increasingly attractive target for cyber threats.
One might not immediately assume that the logistics industry is a valuable target; after all, financial institutions have the money and government entities have the information hackers desire, right? Not quite. In fact, logistics companies manage vast amounts of sensitive data, and private and public entities depend on their operations every single day. These factors make them highly vulnerable to attacks.
How can you address this growing threat?
There is this legendary quote from Sun Tzu on how to overcome your adversaries: 'know thy enemy and know yourself; in a hundred battles, you will never be defeated'. To know your enemy starts with gaining an understanding of yourself, your threat landscape, your adversaries’ intentions, their modus operandi, and specific attacking methods. On this page, the cyber threats to the logistics sector are explored. Understanding the full picture of the challenges our clients may encounter helps us in doing what we do best: ensuring security for your business from specific cyber threats targeting your organization.
Request a free membership to access our full research insights
Already a member? Login here
Threat landscape
For the logistics industry
Advanced Persistent Threats (APTs)
Tactics, Techniques & Procedures (TTPs)
Attack tools
| Logistics | Logistics + related | Broader focus | All known | |
|---|---|---|---|---|
| APTs | 94 | 136 | 193 | 781 |
| TTPs | 1,674 | 1,998 | 2,458 | 4,109 |
| Attack tools | 1,474 | 1,577 | 1,996 | 3,616 |
Logistics faces more cyber threats than ever
To stay in control becomes increasingly difficult
Our proprietary threat diagnostic system shows a discernible increase in malicious activity targeting the logistics sector. As logistics companies race to keep up with rising global demand amid supply chain disruptions, cybercriminals are taking advantage of the pressure. If you operate in the sector, the risks of cyber-attacks, including intellectual property (IP) theft, ransomware, data breaches, and espionage, are escalating, especially if the appropriate defenses are not in place.
Actor overview
The most active attack groups targeting the logistics sector are shown in the dynamic chart highlighting the relationships between the various threat actors, their motivation and their country of origin.
Knowing the APT groups, their motivations and origin countries provides a solid starting point for understanding what you are up against. To get a more comprehensive understanding of the threat landscape, it is important to research, map, and document your adversaries’ intentions to their modus operandi, attack methods and attack tools, as this provides more actionable information for strenghtening your defences.
More detailed information on the threat landscape for this sector?
Already a member? Login here
How it works
Threat landscape for the logistics sector
Attacks in the logistics sector
Look down! Look out! Look up!
The following section explores a few selected cyberattacks in the logistics sector in greater detail. These cases highlight the diverse range of cyber threats affecting the industry across multiple countries and subsectors, with varying tools and impacts. However, they represent only a small fraction of the cyberattacks occurring daily.
January 1, 2022
16:00 PM
Port of Nagoya
2023
In July 2023, the Port of Nagoya -Japan’s largest and most critical port – was crippled by a ransomware attack. The attack was attributed to the notorious LockBit 3.0 group, who were also responsible for a similar incident earlier that year against the Port of Lisbon. Unlike in Portugal, where no operational activities were compromised, the Nagoya attack resulted in the shutdown of the port’s entire network, disrupting communications and bringing import and export operations to a complete halt. Not only were major companies like Toyota directly impacted, but it is also estimated that 10% of Japan’s total trade was disrupted, causing significant economic strain. Nagoya’s response was commendable: isolating affected servers and restoring systems from backups helped minimize long-term damage, and operations resumed after a two-day suspension. However, the attack highlighted the devastating consequences of cyber threats on global supply chains.[1]
January 1, 2022
16:00 PM
Poland Railway
2023
In August 2023, Poland’s railway network – which is pivotal in supplying Ukraine with its weaponry and other resources – faced a severe cyber disruption when attackers hijacked railway frequencies, broadcasting pro-Putin recordings and triggering emergency stoppages.[2] Although services were restored within hours, the incident demonstrated how easily disruptions can bring critical transport infrastructure to a standstill. The ripple effects of such disruptions extend beyond national borders, jeopardizing supply chains that rely on seamless rail operations for cargo movement. This wasn’t an isolated event in the context of the war in Ukraine either. In 2024, GPS interference by Russia disrupted flights over the Baltics and Finland. While the logistics sector may not always be the primary target in the conflict in Eastern Europe, these incidents highlight its vulnerability. Whether through direct attacks or collateral damage, the industry remains at risk.
January 1, 2022
16:00 PM
KNP Logistics
2023
In September 2023, KNP Logistics, one of the UK’s largest and oldest privately owned logistics firms, collapsed under the weight of a devastating ransomware attack. The attack crippled critical systems, compromised financial data, and ultimately left the company unable to secure the investment and funding needed to stay afloat. Within weeks, operations ground to a halt, and over 700 employees lost their jobs.[3] This is the worst-case scenario—a cyberattack so severe that it doesn’t just disrupt business but destroys it entirely. For logistics companies, the stakes couldn’t be higher; a single breach can mean operational paralysis, financial ruin, and the end of decades of business.
Key Trends
for the logistics sector
The threat landscape for the logistics sector is constantly evolving. On one hand, the industry is rapidly digitizing, integrating advanced technologies to optimize efficiency and streamline operations. On the other hand, threat actors are adapting just as quickly, refining their tactics to exploit new vulnerabilities. As logistics companies become increasingly interconnected, they also become more exposed to sophisticated cyber threats. Below are some of the key trends shaping the cybersecurity challenges in the sector today.
The expanding attack surface
Modern logistics operations rely heavily on interconnected technologies. From electronically connected trucks and GPS-dependent fleet management to mandatory electronic logging devices (ELDs) or warehouse management systems, the entire supply chain is now digitized. These technologies not only optimize efficiency but also introduce critical vulnerabilities. Large amounts of (personal) data from truckers, shippers, and vendors are constantly shared across digital platforms, making the industry an attractive target for data breaches and ransomware attacks—the single largest cyber threat facing logistics today.[4]
The growing impact of disruption and costs of cyberattacks
Recent events have highlighted just how fragile the transport ecosystem can be. The COVID-19 pandemic was the single most disruptive event in recent history[5], and more recently, geopolitical incidents such as the 2024 Houthi attacks on vessels in the Red Sea led to a 1.3% decline in global trade. Readers of this page may have even got stranded at an airport for a day or two during the 2024 July CrowdStrike incident, which impacted 8.5 million computers worldwide and was caused by human error. While not cyber, these events demonstrate how disruptions in general can have massive ripple effects on economies.[6]
But cyberattacks aren’t just disruptive—they’re costly. Research by IBM indicates that a single data breach in the transport sector costs organizations an average of $4.18 million.[6] With increasing investments in digital transformation—already leading to a 20% reduction in operating costs over the past few years—businesses can’t afford to ignore cybersecurity. The rise of ransomware, phishing attacks, and supply chain vulnerabilities means that securing digital infrastructure is no longer optional; it’s a necessity.
Global legislative efforts
Recognizing the risks detailed above, governments have taken action. In 2021, then-US President Joe Biden signed an executive order on securing American supply chains, while the NIS2 Directive is being implemented in the EU.[7] Although the latter instrument defines sectors based on slightly different standards, and therefore logistics is not directly mentioned, multiple sectors which can be considered logistics (such as transportation, delivery, or even manufacturing) do fall under NIS2. Furthermore, the directive will require companies to monitor their ICT supply chain’s cybersecurity, further broadening the scope of mandatory cybersecurity measures across the Union.
How to defend yourself
threat model approach
To defend against this threat landscape, it is equally important to gain critical insights into the current resilience level of your organization. To understand thyself it is useful to let (third-party) security specialists assess your defenses and simulate meaningful attacks. When done right, such an approach provides critical insights into the resilience level of the organization against its threat landscape. Hunt & Hackett use its proprietary threat modelling-based approach with its clients in the logistics sector to provide meaningful insights as well as tailored solutions for the strategical, tactical, and operational aspects of their cybersecurity program.
Our approach
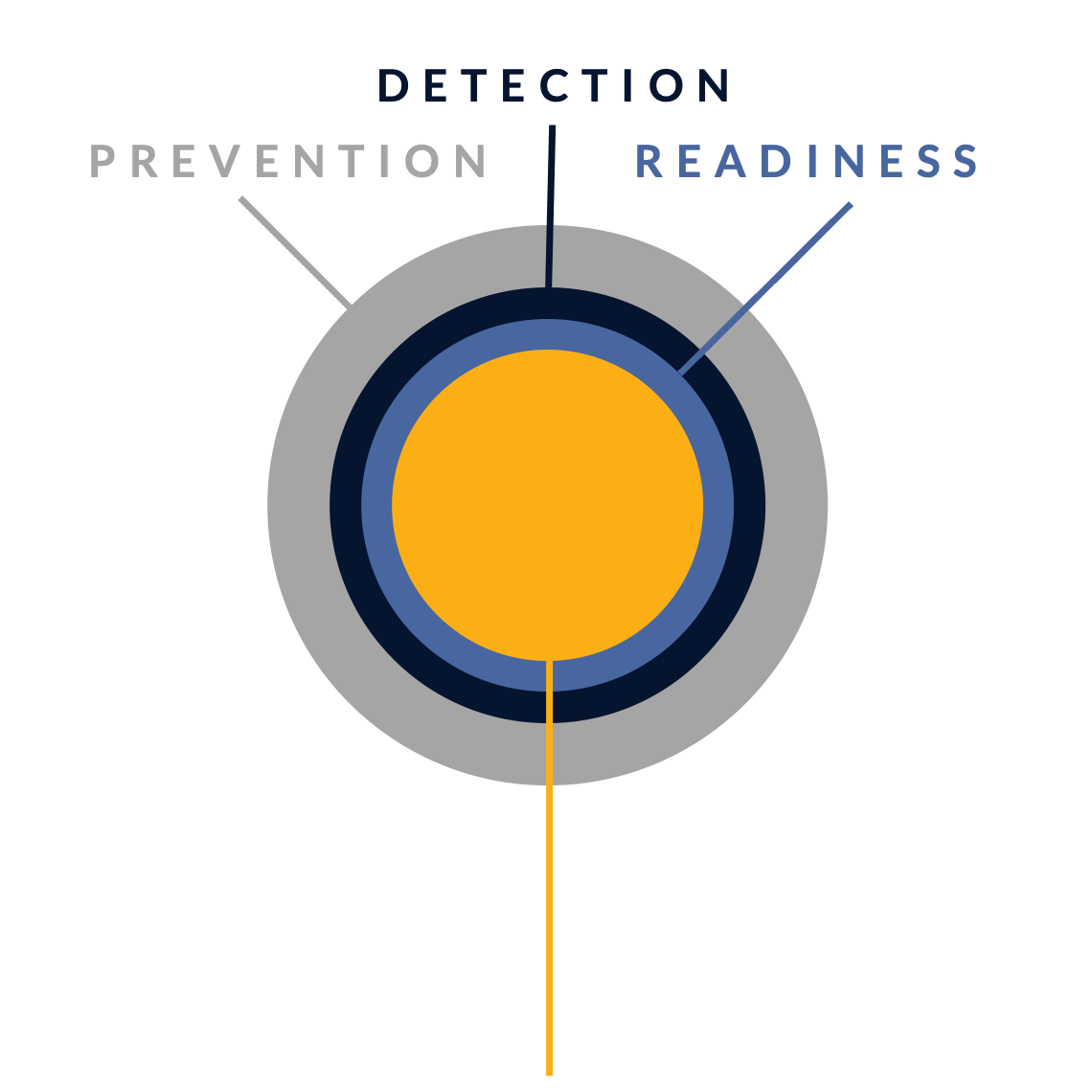
Controlling your cybersecurity risks
In their fight against cyber attacks, our customers typically go through several stages of maturity. By ramping up their prevention, detection and incident readiness over time – and optimizing this for their actual threat landscape – they reach a point where they have developed solid resilience against targeted attacks, with only highly controlled and accepted risks remaining.
There is no simple 'fix' to become resilient against the sophisticated cyber threats of today. Without serious resources or processes for systematic security activities, protection against modern cyber threats like ransomware is just a wish. Hunt & Hackett has developed a unique threat- and sector-driven approach to cybersecurity, enabling you to work from your current situation to a highly improved and controlled situation, optimized for your specific threat landscape and context as an organisation.
STAGE 1: Unknown risk
Pre-monitoring
-
STAGE 2: Reduced risk
Post-monitoring
-
Detection & response controls
Resilience against non-targeted attacks

STAGE 3: Controlled risk
Implemented roadmap
-
Resilience against non-targeted and semi-targeted attacks
STAGE 4: Highly controlled risk
Targeted attack resilience
-
Our services
Optimized for the logistics sector
Because we use your actual threat landscape and your sector as our starting points, our services are optimised for your specific context and needs.
Managed Detection & Response (MDR)
We detect & react to attacker activity in your environment, minimizing the impact on your business.
Security Program Gap Assessment (SPGA)
We assess your current security program, threat landscape, security controls and risk.
Incident Response (IR)
We help you manage a cyber crisis and contain security incidents, breaches and cyber threats.
Breach & Attack Simulation (BAS)
We validate your security choices by simulating attacks.
Our articles about the logistics sector
From Hunt & Hackett experts
References
1. https://www.bbc.com/news/world-europe-66630260
3. https://www.dragos.com/blog/ot-cybersecurity-breach-disrupts-operations-at-the-port-of-nagoya-japan/
5. https://edgelabs.ai/industries/transportation-and-logistics/
6. https://www.weforum.org/stories/2024/06/transport-supply-chain-ecosystems-cyber-resilience/
7. https://www.iea.org/policies/15272-executive-order-14017-of-americas-supply-chains