Cybersecurity for the Technology sector
The technology sector is one of the fastest growing and most influential industries in the world. It continues to expand rapidly, driven by the demand for AI, computing power, electronics, and a wide array of digital services, including Cloud providers, SaaS, PaaS, IaaS platforms and collaboration tools. The sector includes a diverse range of organizations, each contributing to the digital backbone of modern society. Despite their differences, these companies share a common vulnerability: exposure to cyberattacks.
In recent years, Hunt & Hackett has seen a clear increase in activity by Advanced Persistent Threat (APT) groups targeting the technology sector. The combination of cutting-edge innovation and access to sensitive data makes these companies attractive to adversaries focused on espionage, financial gain, or intellectual property theft. And beyond that, tech companies often serve as intermediaries to a large set of underlying organisations or individuals. This makes them attractive targets for supply chain attacks—as seen in cases like the Snowflake (2024), Microsoft Exchange (2021), and SolarWinds (2020) attacks. As these incidents demonstrate, successful attacks on technology firms can have far-reaching and serious consequences.
How can you address this growing threat?
There is this legendary quote from Sun Tzu on how to overcome your adversaries: 'know thy enemy and know yourself; in a hundred battles, you will never be defeated'. To know your enemy starts with gaining an understanding of yourself, your threat landscape, your adversaries’ intentions, their modus operandi, and specific attacking methods. On this page, the cyber threats to the technology sector are explored. Understanding the full picture of the challenges our clients may encounter helps us in doing what we do best: ensuring security for your business from specific cyber threats targeting your organization.
Request a free membership to access our full research insights
Already a member? Login here
Threat landscape
For the technology industry
Advanced Persistent Threats (APTs)
Tactics, Techniques & Procedures (TTPs)
Attack tools
| Technology | Technology + related | All known | |
|---|---|---|---|
| APTs | 439 | 476 | 801 |
| TTPs | 2,907 | 3,378 | 4,112 |
| Attack tools | 2,585 | 2,905 | 3,666 |
Technology faces more cyber threats than ever
To stay in control becomes increasingly difficult
Our proprietary threat diagnostics system shows a significant increase in malicious activity targeting the technology sector. As digital innovation accelerates, so do the risks. The sector continues to attract financially motivated cyber criminals and nation-state actors alike. They are drawn by its access to sensitive data, intellectual property, its strategic role across industries, and by its role as a conduit to other organisations through interconnected supply chains. This, combined with the frequent adoption of new technologies, reliance on third-party providers, and widespread use of cloud services, has significantly expanded the attack surface. High-profile breaches in recent years demonstrate how vulnerabilities can be exploited at scale and how quickly attacks can spiral across interconnected systems. As organizations struggle to keep pace, staying in control becomes more challenging.
However, understanding who is targeting your business provides a crucial advantage. Each threat actor has different goals, tactics, and preferred entry points. Knowing your adversaries allows for smarter defenses, better prioritization, and a stronger security posture overall. The following overview outlines the actors most active in the technology sector today.
Actor overview
The most active attack groups targeting the technology sector are shown in this chart highlighting which motivations are driving the various actors active in this sector.
Knowing the APT groups, their motivations and origin countries provides a solid starting point for understanding what you are up against. To get a more comprehensive understanding of the threat landscape, it is important to research, map, and document your adversaries’ intentions to their modus operandi, attack methods and attack tools, as this provides more actionable information for strenghtening your defences.
More detailed information on the threat landscape for this sector?
Already a member? Login here
How it works
Threat landscape for the technology sector
Attacks in the technology sector
Look down! Look out! Look up!
This section explores several major cyberattacks that have impacted the technology sector in the 21st century. As one of the most frequently targeted industries, tech companies face unique risks due to their broad digital footprint, central role in global infrastructure, and often interconnected services. The incidents highlighted here illustrate just how far-reaching the consequences can be: from regulatory penalties to reputational damage and operational disruption. While these examples offer a window into the threat landscape facing tech firms, they represent only a small subset of the cyber activity taking place across the sector. The true scale of attacks remains vast, often unfolding quietly behind the scenes.
January 1, 2022
16:00 PM
Snowflake data breach
2024
In mid-2024, Snowflake, a major cloud data warehousing provider, was at the center of a widespread data breach that exposed customer environments across at least 165 organizations. The intrusion was attributed to UNC5537, a financially motivated threat actor who systematically accessed customer instances using stolen credentials harvested through infostealer malware. These credentials, many of which had remained active for years without rotation or multi-factor authentication, enabled unauthorized access and large-scale data exfiltration. Snowflake's core infrastructure was not compromised, but the breach revealed significant lapses in access control enforcement among its customer base.[1] High-profile victims included AT&T, Santander, Ticketmaster, and Advance Auto Parts. AT&T reportedly paid $370,000 in an effort to contain the fallout.[2]
The campaign operated quietly over time, using standard administrative tools to perform reconnaissance and extract sensitive data, which was later advertised for sale on cybercriminal forums. The actor behind the operation, known online as “Judische,” was arrested in Canada in October following a coordinated law enforcement investigation.[3] The incident demonstrated the scale of damage possible when credential hygiene and third-party access are not adequately managed. It also showed how compromise at a single technology provider can lead to widespread downstream impact, highlighting the real-world consequences of supply chain exposure, even in the absence of direct infrastructure compromise.
January 1, 2022
16:00 PM
T-Mobile
2021 - 2023
Between 2021 and 2023, T-Mobile experienced a series of significant data breaches that exposed the personal information of tens of millions of people. The largest occurred in August 2021, when a threat actor claimed to possess data on 100 million individuals. T-Mobile confirmed the breach shortly after, estimating that 76 million customers were affected. The stolen information included names, phone numbers, addresses, Social Security numbers, and PINs: data that enabled identity theft, phishing attempts, and account takeovers.[4] The 2022 and 2023 incidents involved credential theft, phishing attacks on employees, and API exploitation due to misconfigured access controls. One breach in early 2023 allowed attackers to access account data of 37 million customers via automated queries submitted through a vulnerable API.
In 2024, T-Mobile reached a settlement with the Federal Communications Commission that included a $15.75 million civil penalty and a binding agreement to invest an additional $15.75 million over two years to improve its cybersecurity resilience.[5] The T-Mobile breaches underscored the risks of poor access control, inconsistent incident response, and technical debt.
January 1, 2022
16:00 PM
Microsoft Exchange Server
2021
In early 2021, Microsoft disclosed a global cyberattack exploiting four zero-day vulnerabilities in its on-premises Exchange Server software. The state-sponsored Chinese group HAFNIUM was identified as the primary actor, leveraging flaws (CVE-2021-26855, CVE-2021-26857, CVE-2021-26858, and CVE-2021-27065) to access email accounts, elevate privileges, and install web shells: tools allowing persistent backdoor access.[6] The attack began as early as January and impacted over 250,000 servers worldwide, including those of law firms, universities, think tanks, and government agencies. While patches were released on March 2, many systems remained vulnerable as attackers raced to exploit unpatched servers. The attack demonstrated how Exchange servers – central to enterprise communication – could become launchpads for broader network compromise. Threat actors extracted emails, passwords, and in some cases installed ransomware like DearCry. Despite Microsoft's mitigation tools, backdoors often remained after patching.[7]
A later attack in 2023, targeting Exchange Online, prompted a damning 2024 review by the U.S. Cyber Safety Review Board. It found Microsoft’s security culture lacking, citing delayed detection, premium logging restrictions, and weak risk management. The board deemed the breach “entirely preventable” and called for sweeping reforms at not just Microsoft, but across cloud infrastructure providers.[8] The Exchange hacks served as a wake-up call for the risks of concentrated digital dependencies and illustrated how a compromise in widely used platforms can cascade across countless organisations, amplifying the kind of systemic exposure typical of supply chain attacks.
January 1, 2022
16:00 PM
SolarWinds
2020
In 2020, attackers linked to Russia’s Foreign Intelligence Service carried out one of the most sophisticated supply chain attacks in history, targeting IT management software provider SolarWinds. The breach originated from malicious code inserted into an update for the company’s Orion platform, a tool widely used for network monitoring and infrastructure management. Once deployed, the compromised update provided attackers with a hidden backdoor, giving them remote access to customer systems. Nearly 18,000 organizations downloaded the tainted software, including major tech firms like Microsoft, Intel, and Cisco, as well as U.S. federal agencies such as the Department of Homeland Security and the Department of Energy. While only a smaller group of high-value targets were actively exploited, the intrusion enabled deep network access and months-long espionage.[9]
The SolarWinds incident underscored how vulnerable the software supply chain has become. Trusted vendor relationships, especially in the technology sector, can quickly become single points of failure, allowing attackers to pivot from one target to many. As a result, the breach sparked widespread calls for improved supply chain security and tighter scrutiny of third-party software providers. To learn more about how the SolarWinds attack could have been prevented, read our blog post.
January 1, 2022
16:00 PM
2018
In late September 2018, Facebook suffered its first major hack since its launch, when attackers exploited a flaw in the “View As” feature to steal access tokens: digital keys that allow users to stay logged in without reentering credentials. Initial reports indicated up to 50 million accounts were compromised, with Facebook forcing 90 million users to log out as a precaution. The stolen tokens also posed a risk to any third-party app using Facebook’s single sign-on (SSO), such as Spotify and Airbnb. Researchers warned of a cascading security threat, as a compromised social login could unlock dozens of connected services. Facebook rapidly patched the vulnerability, disabled the feature, and reset millions of tokens. They notified law enforcement and users, but didn’t confirm any misuse of specific accounts.[10]
The incident highlighted two major risks: how deeply integrated social logins increase attack surfaces, and how quickly large-scale vulnerabilities can spread. In 2024, EU regulators fined Meta €251 million under GDPR law, finding only 29 million accounts were impacted in Europe, but pointing to systemic failures in safeguarding user data.[11]
January 1, 2022
16:00 PM
Yahoo
2013 - 2014
In what remains the largest known data breach in history, Yahoo confirmed in 2017 that all 3 billion user accounts had been compromised during a 2013 cyberattack. The stolen data included names, email addresses, phone numbers, birth dates, and hashed passwords, along with security questions and answers - some of which were unencrypted.
Yahoo initially disclosed the breach in 2016, estimating 1 billion affected users. A year later, that number was revised; tripling in scale after further forensic analysis.[12] The delay in full disclosure drew sharp criticism from regulators and cybersecurity experts, particularly since Yahoo had also suffered a separate breach in 2014 that compromised an additional 500 million accounts. That attack was believed to have been orchestrated by Russian state-sponsored hackers attempting to spy on U.S. targets.[13] So why wasn’t the 2013 breach disclosed earlier? At the time, Yahoo was in the process of finalizing the sale of its core business to Verizon Communications, Inc. When the breach became public in 2016, Verizon negotiated a $350 million reduction in the acquisition price, citing concerns over brand damage and legal liability. Yahoo also faced lawsuits, intense public backlash, and a $35 million fine from the SEC for failing to disclose the breach in a timely manner.[14]
Together, these incidents underscore how poor breach visibility and delayed reporting can devastate a company’s reputation and directly affect its valuation.
Key Trends
For the technology sector
Few industries move as fast or are as interconnected as the technology sector. As the engine powering innovation across virtually every modern industry, tech firms play a pivotal role in enabling global progress. From cloud services to collaboration tools, from semiconductors to AI platforms, the sector creates and maintains the digital backbone of the modern economy. But with that influence comes risk. As early adopters of new technologies and frequent targets of cyber espionage, tech companies face unique cybersecurity challenges that evolve just as quickly as the tools they build.
This section outlines four key trends shaping the cybersecurity landscape for the technology sector:
Innovation brings risk: the cyber trade-off of early adoption
Tech companies thrive on experimentation. As leaders in research and development, they are often the first to explore new technologies, be it AI, IoT devices, or emerging platforms for communication and collaboration. This early adoption can be a competitive advantage, but it also introduces new vulnerabilities. Unproven tools often lack mature security controls and newly discovered bugs or zero-day exploits can go unpatched for weeks or even months.
This appetite for innovation expands the attack surface, particularly when staff rely heavily on interconnected apps, mobile devices, and cloud-based collaboration tools. Even in highly technical environments, human error remains a major risk. Social engineering attacks, especially sophisticated spear phishing campaigns, can still compromise even the most digitally literate teams.[15]
Cloud-first strategies demand robust security practices
As remote work, global teams, and agile development become standard, the cloud has become essential infrastructure. Many tech companies now operate in cloud-native or hybrid environments that offer unmatched scalability and flexibility. But this convenience also comes with pitfalls.
Cloud misconfigurations remain one of the most common and costly cybersecurity issues. A single exposed database or weak API security can grant attackers access to sensitive data. Additionally, cloud service providers themselves are high-value targets: a breach at one provider can cascade into multiple client networks. To secure their environments, tech firms must implement strong access controls, continuous monitoring, and a deep understanding of shared responsibility models.[16]
Supply chain attacks continue to rise, escalating damage and reputational risk
Software supply chain attacks surged in April and May 2025, with recent months averaging nearly 25 incidents—almost double the previous rate. In the first five months of the year, 63% of such attacks directly targeted IT, technology, and telecommunications companies, making downstream users especially vulnerable.[17] A single compromise, as seen in recent ransomware campaigns, can impact hundreds of businesses. The potential for operational disruption and reputational damage is immense. As organizations increasingly depend on interconnected platforms, even non-tech industries face heightened risk through third-party providers. The growing scale and sophistication of these attacks highlight the urgent need for stronger supply chain controls.
Sensitive data and valuable IP make tech firms prime targets
Tech companies manage vast stores of sensitive data: customer records, proprietary algorithms, financial data, and trade secrets. The latter, for example, makes them attractive targets for both cybercriminals and nation-state actors seeking valuable intellectual property (IP). Stolen IP can erode competitive advantage, allowing rivals to replicate innovations without the investment in R&D. Meanwhile, the theft of personally identifiable information (PII) increases the risk of identity theft, fraud, and further social engineering attacks. As demonstrated by high-profile breaches in recent years, the consequences of losing this kind of data can be devastating; impacting not just company valuations, but national security.
NIS2 Compliance
For essential and important entities
Companies in the technology sector may fall under the scope of the NIS2 Directive as Essential or Important entities. Organizations are expected to address several important aspects of cybersecurity, as outlined in Article 21(2) of the Directive, including:
- Awareness of your threat landscape and a data-driven security roadmap.
- Risk analysis and security policies to safeguard information systems.
- Incident handling and business continuity to ensure resilience and recovery.
- Forensic readiness and the ability to perform a root cause analysis.
- Supply chain and system security for robust protection and secure development.
Hunt & Hackett’s Managed Detection and Response (MDR) solution directly aligns with several of the Directive’s key requirements, including the 24-, 72-, and one month incident reporting timelines, forensic readiness requirements, and risk management preparation. Read on to discover the core features of our service.
We've also developed a practical assessment framework that aligns NIS2 requirements with established cybersecurity standards, including ISO/IEC 27001:2022, ISO/IEC 27002:2022, and CIS controls. Although exact NIS2 requirements are evolving, our standards-based approach provides a robust foundation to benchmark your current cybersecurity measures and pinpoint areas for improvement.
How to defend yourself
Threat model approach
To defend against this threat landscape, it is equally important to gain critical insights into the current resilience level of your organization. To understand thyself it is useful to let (third-party) security specialists assess your defenses and simulate meaningful attacks. When done right, such an approach provides critical insights into the resilience level of the organization against its threat landscape. Hunt & Hackett use its proprietary threat modelling-based approach with its clients in the technology sector to provide meaningful insights as well as tailored solutions for the strategic, tactical, and operational aspects of their cybersecurity program.
Our approach
Controlling your cybersecurity risks
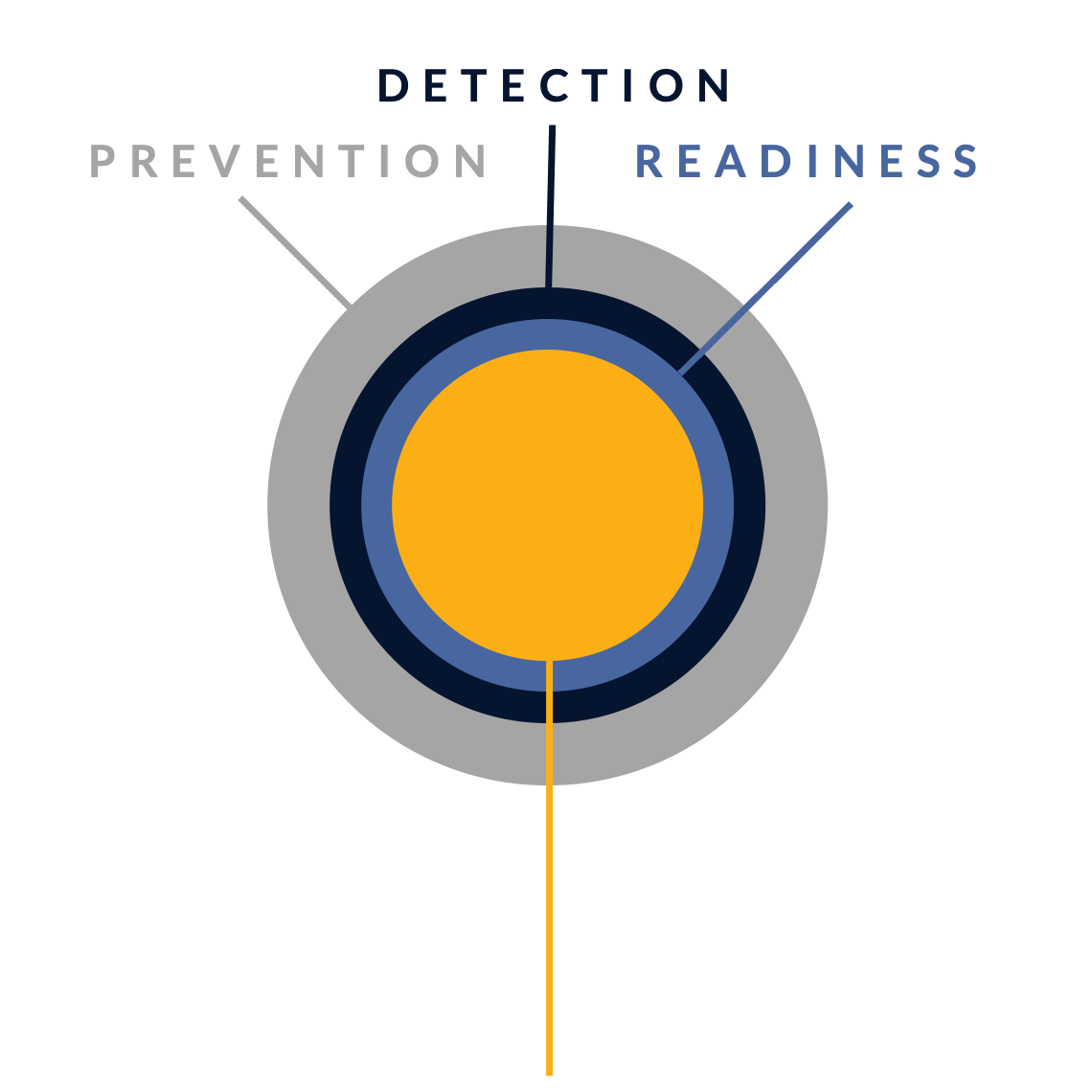
In their fight against cyber attacks, our customers typically go through several stages of maturity. By ramping up their prevention, detection and incident readiness over time – and optimizing this for their actual threat landscape – they reach a point where they have developed solid resilience against targeted attacks, with only highly controlled and accepted risks remaining.
There is no simple 'fix' to become resilient against the sophisticated cyber threats of today. Without serious resources or processes for systematic security activities, protection against modern cyber threats like ransomware is just a wish. Hunt & Hackett has developed a unique threat- and sector-driven approach to cybersecurity, enabling you to work from your current situation to a highly improved and controlled situation, optimized for your specific threat landscape and context as an organisation.
STAGE 1: Unknown risk
Pre-monitoring
-
STAGE 2: Reduced risk
Post-monitoring
-
Detection & response controls
Resilience against non-targeted attacks

STAGE 3: Controlled risk
Implemented roadmap
-
Resilience against non-targeted and semi-targeted attacks
STAGE 4: Highly controlled risk
Targeted attack resilience
-
Our services
Optimized for the technology industry
Because we use your actual threat landscape and your sector as our starting points, our services are optimised for your specific context and needs.
Managed Detection & Response (MDR)
We detect & react to attacker activity in your environment, minimizing the impact on your business.
Security Program Gap Assessment (SPGA)
We assess your current security program, threat landscape, security controls and risk.
Incident Response (IR)
We help you manage a cyber crisis and contain security incidents, breaches and cyber threats.
Breach & Attack Simulation (BAS)
We validate your security choices by simulating attacks.
Our articles about the technology sector
From Hunt & Hackett experts
References
- https://cloud.google.com/blog/topics/threat-intelligence/unc5537-snowflake-data-theft-extortion
- https://www.wired.com/story/atandt-paid-hacker-300000-to-delete-stolen-call-records/
- https://thehackernews.com/2024/11/canadian-suspect-arrested-over.html
- https://www.forbes.com/sites/steveweisman/2025/05/18/checks-being-sent-to-victims-of-t-mobile-data-breach/
- https://www.cybersecuritydive.com/news/fcc-settlement-t-mobile-data-breaches/728543/
- https://www.microsoft.com/en-us/security/blog/2021/03/02/hafnium-targeting-exchange-servers/
- https://socradar.io/microsoft-exchange-server-cyberattack-timeline/
- https://www.ic3.gov/CSA/2021/210310.pdf
- https://www.gao.gov/blog/solarwinds-cyberattack-demands-significant-federal-and-private-sector-response-infographic
- https://www.theguardian.com/technology/2018/sep/28/facebook-50-million-user-accounts-security-berach
- https://www.euronews.com/business/2024/12/17/facebook-owner-meta-hit-with-251m-fines-bill-for-2018-data-breach
- https://www.reuters.com/article/technology/yahoo-says-all-three-billion-accounts-hacked-in-2013-data-theft-idUSKCN1C82NV/
- www.nytimes.com/2017/10/03/technology/yahoo-hack-3-billion-users.html
- https://www.sec.gov/newsroom/press-releases/2018-71
- https://www.isaca.org/resources/news-and-trends/newsletters/atisaca/2024/volume-9/eight-overlooked-emerging-tech-risks-and-how-to-mitigate-them
- https://technologymagazine.com/articles/how-cloud-security-risks-soar-and-threaten-business
- https://cyble.com/blog/supply-chain-attacks-surge-in-april-may-2025/